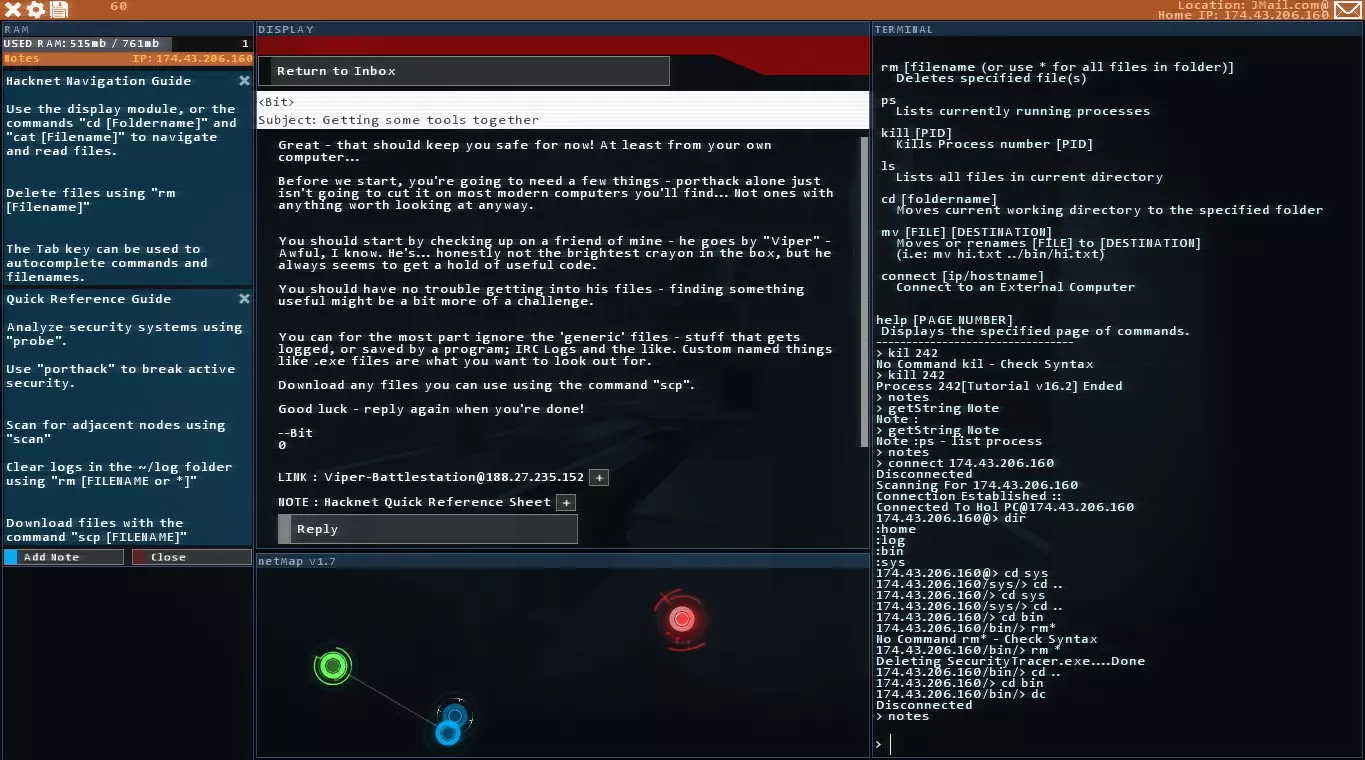
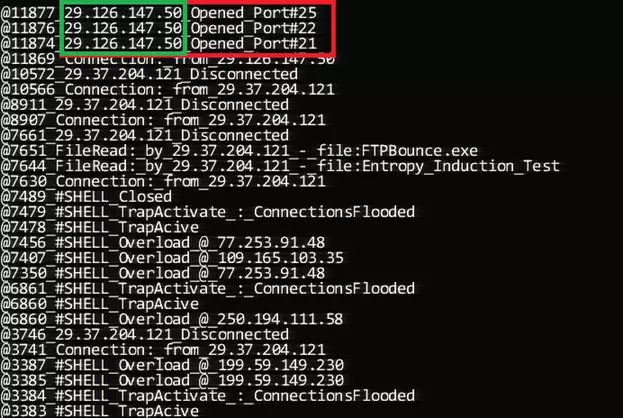
Full spread with pre-requirements for completing successfully the bit missions and finnishing the game. Prequisites For successfully completing the mission you will need the following programs on your local bin folder: SSHcrack.exe (first program achieved on bit's requests at the start of the game) FTPBounce.exe (second program achieved after completing the "Entropy registration" contract) eosDeviceScan.exe (third program achieved after recieving the "eOS device scanning" contract) SMTPoverflow.exe (fourth program achieved after you recieve the contract of "Agression must be punished") WebServerWorm.exe (fifth program achieved after you have naix's secondary relay server [from where he attacks you]) Sequencer.exe (sixth program achieved after you get accepted in CSEC) SQL_MemCorrupt.exe (seventh program achieved after you get accepted in CSEC) Decypher.exe (eigth program achieved in the "Ghosting the vault" contract) DECHead.exe (ninth program achieved in the "Through the Spyglass" contract) KBT_PortTest.exe (tenth program achieved in the "Project Junebug" contract) TraceKill.exe (eleventh program achieved in the start of bit's missions sent by "V") Another way to get the KBT_PortTest.exe after you have started bit's mission.Hack into the Universal Medical Server, search for a patient with "Whit Elliot", and then in the record find the "documentation and notes" IP. Here is the ip if you can't find it: 66.96.147.84. When you enter that server, click exit and hack the system. Firewall Solution For the server at 66.96.147.84 and it's adjecent one: BIOGEL. Once you are through, type scan and you will get another server (dont forget to delete your logs). Connect to that other server and hack it also, after you are through use "cd home/Production/Output" and copy the exe to your computer, then disconnect (dont forget to delete your logs here either). Now you have the tenth program ready. V - Bit -- Foundation This is the start of the missions, and it is simple, you download the TraceKill.exe after decompressing it with the given password dx122DX. once you have downloaded it, you just reply to the mail to continue with the missions. V - Bit -- Substantiation In here you have to connect to Bit's repo base (NOTE: TraceKill uses 600MB of ram, so if you want to stop the tracing you will have to get the ram free'd up and then run it [if you are running out of time after you have found the password {due to its long time to shutdown} simply shut it down manually with [b]"ps"[/b] and then "kill [PID]".]) Step 1: Hacking the systemStart by probing and getting the ports available for hack. You will have to hack/disable the following: (NOTE: You only need to open 4 ports to run porthack here) Proxy (overloading it with shelled computers) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) SQL Server (SQL_MemCorrupt in console, default port 1433) SMTP MailServer (SMTPoverflow in console, default port 25) FTP Server (FTPBounce in console, default port 21)If you do it fast, you should have some 30-40 trace time left, so run TraceKill as fast as possible for an extra time while you are in the server. In the server, you need to go to the directory ("cd home/work") home and then go in the work folder and copy the file in there. Disconnect and close tracekill and go to your pc, then analyze the .DEC file you just downloaded with DECHead. You will get an ip, put it in your notes or memoryze it, then reply to V with the IP adress. V - Bit -- Investigation You will recieve a mail from bit with another server, connect to that server, it's the main website of "EnTech". Start by probing and getting the ports available for hack. You will have to hack the following: (NOTE: You only need to open 4 ports to run porthack here) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) SQL Server (SQL_MemCorrupt in console, default port 1433) SMTP MailServer (SMTPoverflow in console, default port 25) FTP Server (FTPBounce in console, default port 21)After you are through (and porthack has shut down) run tracekill to get again some extra time. Start by scanning for linked computers, you will get 3 computers ("ZEUS", "WORKSTATION_CORE", "MAIL"), delete the logs (or have some fun around editing the website page cause you can) and disconnect from it (also shutdown tracekill after you disconnect). ZEUS and the MAIL servers are INVIOABLE so you can't hack them, you can only log in if you have the password, however you can hack the WORKSTATION_CORE. Probe the WORKSTATION_CORE. You will have to hack the following: (NOTE: Tracing here is very fast, so after you get the password manually kill porthack process and run tracekill as fast as you can) SQL Server (SQL_MemCorrupt in console, default port 1433)After you get the password and get tracekill active, scan the network for linked computers and delete your logs, then disconnect and shutdown tracekill. On the scan you will get 5 servers listed, 4 of them have the INVIOABILITY detection warning, but one of them doesn't. Connect to that sysem and probe it. You will need to hack the following: Proxy (Overloading with shelled computers) Firewall (Solution: BEKX4S [EDIT: According to a comment this now changes. You will have to figure this one out on your own if so.]) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) Medical Services (KBT_PortTest in console, default port 104)Once you have hacked through and activated tracekill, navigate to workstation > store ("cd workstation/store") and read "StoreServIPs.txt" to get the ips of the PROMETHEUS and ROMULUS servers. write both of them down in your notes, then read the file "Prometheus.txt" for the password to access the PROMETHEUS server. Once you have done this, disconnect (because there are no more linked computers to that last server) and reply to V's mail. (NOTE: if you can't reply to V's mail because it says mssion incomplete after following this whole secton from top to bottom, then check that the last mail that you recieved is V's mail about investigating bit's case, however, if it still doesn't let you reply, connect to the PROMETHEUS server and log in, at that point V should send you a mail back automatically.) V - Bit -- Propagation You will recieve another e-mail with a link back to the first found INVIOABLE system. Ignore it for now, you have to do something else first. Connect to the Prometheus server that you remembered/placed on your notes, log in with username: admin and the password that you also remembered/placed on your notes. Once you are in, delete the logs and run eosDeviceScan, you will find 2 linked phones. Connect to the first phone, and log in with the username: admin and password: alpine and go into the mail folder under /eos and write down in the notes the account username (what goes before the @) and also the password for the account. Disconnect from the phone and connect to the MAIL server of EnTech, log in with the username that you wrote down and the password for it. Once you are in the e-mail, read the mail that says "Re: Romulus passwd", copy down on your notes the password and disconnect from the mail server. Now that you have the ROMULUS password, connect to the romulus server and log in to it with the username: admin and the password that you placed on your notes. Go into the file system data and find a file under STORE/contractors named Contractor_Server.doc, read it and there should be a password again, write it down in your notes and disconnect from there. From here you can choose to go into the relay server (that V linked you and that is linked in the doc file) or reply to him with the password, you choose. V - Bit -- Vindication This part is simple, you get a mail from V telling you the password of a .DEC encrypted file in the EnTech Relay server. Decrypt the file if you want and then reply to V. V - Bit -- Termination This one will be a complicated and fast paced one, better read the guide first unless you know how to do it. PrequisitesGet some shelled computers ready (I normally use 6 for a fast proxy disabling). Step 1(NOTE: if you do not have Sequencer.exe downloaded, go grab it from the asset server.) Activate Sequencer.exe and click activate. Step 2You will be automatically connected to the offline server and you will be moved into the probe page automatically. You will need to hack the following: (NOTE: You need to hack it ALL to run porthack) Proxy (Overloading it) Firewall (Solution: [EMMETPLACE]) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) SQL Server (SQL_MemCorrupt in console, default port 1433) SMTP MailServer (SMTPoverflow in console, default port 25) FTP Server (FTPBounce in console, default port 21) Medical Services (KBT_PortTest in console, default port 104) Step 3Once you are in, you will have to navigate in the server ARCHIVE -> Hacknet and enter folder by folder and delete all the files in each with "rm *" Once you are done deleting that, delete your logs and ready up ForkBomb to launch it once log deletion is complete. You should be done with this and Sequencer should automatically close. Video Version:
步骤4:回复V的邮件,你会收到一封任务完成邮件。 比特-终端 这是“完成”游戏前的最后一个任务。




 换一换
换一换