Hacknet



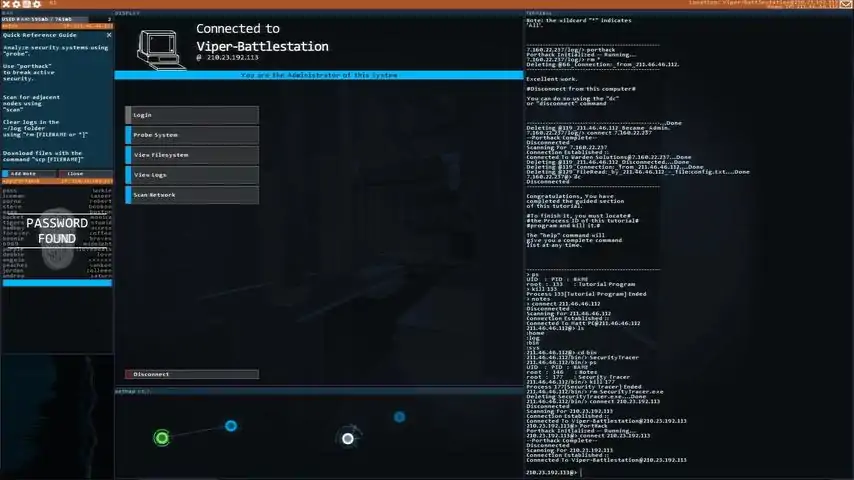

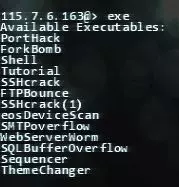
(译者:由于我才疏学陋,翻译时有不准确的地方,有能力者还请参考原版攻略。 任务名、软件名等英语专用名暂时不予翻译,但部分会在后面附上解释,服务器名等请借助工具书。 (此条过期)据悉,目前游戏所有文本已翻译完成,正在校对。预计8/15校审完成,8/20提交至游戏作者。 欢迎加入Hacknet吧正式Mod研究所,群号码:583218698。() 我在指南下看见很多卡关的玩家,但因技术问题在这里我难以给出回复。故请卡关的玩家到贴吧/steam论坛提问,或到上面所写的群中寻求帮助。 ) 由 [Cash.net] Gorimaccha 制作 I made this guide for those who think they're completely stuck. I don't recommend you to read this too much if you seek some challenge :) All missions available now! 这个攻略提供给那些完全卡关的玩家。过分阅读可能影响您的游玩体验。(*剧透警告*) Basic Tips 基础窍门 ***IMPORTANT*** Some computers/servers may have different names on them, but what you need to do should be the same. Just follow the steps, you will be fine. ***非常重要*** 有些电脑/服务器可能有不同的名字,但你所要做的应该相同。遵循如下步骤,您就不会有问题。 DON'T abandon any missions atm!! It will most likey cause serious problems and make you unable to finish the game! 眼下,***请勿***放弃任何任务!!这很可能导致严重问题并最终无法完成游戏,毁掉您的存档! 1, Type commands as soon as possible. 2, Delete logs when you disconnect. 3, You need to reply almost every time you finish a mission. 4, Always use "Scan Network" option when you successfully hack a computer. 5, Don't delete/rename files unnecessarily. <-This is important!! 6, Use auto-complete for commands and file names. (Tab key) 7, Always use "admin" "alpine" to log in to any eos devices. 1.尽速输入指令。(译者:更要善用Tab) 2.断线前别忘了删log。(译者:虽然我不删也没有什么麻烦……) 3.不要忘了完成任务时回复邮件。(极少数情况不需要) 4.成功骇入电脑时总扫描一遍主机。(译者:★★★★★推荐) 5.无必要时不要删除/重命名任何文件!<—十分重要。 6.使用“自动拼写”(Tab键)输入指令及文件名。 7.不要忘了“admin”“alpine”这神奇的eos设备账户。 译者:即使你希望独立完成游戏,我也非常推荐您阅读这些提示,它们非常有用。另外我在此补充几条。 (但愿我没记错……) 1.SQL的入侵工具和KBT,即104端口入侵工具可以忽视Proxy和Firewall。 2.Firewall和Proxy的破解是独立的,你可以一边破解proxy一边analysis。更有甚者,用Tracekill可以允许您慢悠悠地破解完Firewall,再攻破proxy。 3.在shell里按overload破解proxy,对吧?然而如果内存不足,这些窗口会折叠,并在内存足够时展开。(如果我说的不清楚,可以试着在您的电脑上运行一堆shell并点按trap,然后关掉其中一个窗口。)除了略有点壮观以外,这是个“储存”足够多shell的小技巧。 4.不过,5~7个shell一般够了。 5.在几次analyze后弹出的几行文字里应该会各有一个字符,如果某一行里全是”0”怎么办?有时这意味着所对应的代码就是0。例如:(只是示范) 0 0 0 0 0 0 0 0 0 0 2 0 0 0 0 0 0 0 0 5 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 结果就是250。(我才不是250呢!) Troubleshooting Common Problems Q, I don't get an email to start a new mission!! What do I do now!? A, Make sure to check following things: 1, Your previous mission has finished. (Click "Reply" in the email for it and see if "Mission Incomplete" message shows up.) 2, You don't have any available missions in your current faction's contracts server. (Or the message board if you're working on /el missions.) 3, Restart your game and your problem is still there. 常见问题解决方案。(疑难杂症) Q:我得不到开始新任务的邮件!!我该怎么办! A:出门检查您的邮筒(划掉)。请确认您已检查过以下条件。 1.你上一个的任务已完成。[尝试点按邮件中的“Reply”(回复)看会不会出现“Mission incomplete”(任务未完成)。] 2.在您现在所处的派系(Entropy,CSEC,…)没有可用的任务,或者 在/el任务里信息板上没有任务。 3.重启游戏问题仍存在。 For "gg wp" from Naix, you need to revenge Naix BEFORE you start any new Entropy mission. Details in "Naix Missions" section below. 对于Naix的“友善问好”,你要在完成Entropy任务***之前***对Naix报仇。下面的“Naix任务”一栏会给您帮助。 If none of these helps you, you might have had a critical bug... The devs are working on an update to fix many bugs, so wait for it... Meanwhile, you still can try 2 options: 1, Editing your save data (Here's the link: http://steamcommunity.com/sharedfiles/filedetails/?id=500893610 Be super careful with your savedata.) 2, Start a new session (This is much easier... You also can work on achievements that you missed.) 若以上几条都不起作用,您已无药可救了(划掉)。您可能遇到了一个严重的bug(您不会连bug也不知道吧?)。开发者们(们?)在致力于更新游戏以修正bug。所以只能等了。 在此时,您可以尝试以下方法。 1.编辑您的存档。(敬参阅http://steamcommunity.com/sharedfiles/filedetails/?id=500893610请特别小心对待您的存档) 2.再开个存档。(不仅简单多了,还可以去做您以前忽略的成就。) Q, I don't have the necessary exe file to do this mission!! UGGHHHH A, Here is the list of exe files, and in which mission you can find them. Use "CTRL+F" on this guide and search for them. Q.我怎么没有做任务所需的工具!!啊啊啊!! A.这是exe文件列表及其来源,用"CTRL+F"在这指南里搜索一下。 SecurityTracer.exe - "First Contact", or on "Credit Server" after you finish the game. SSHcrack.exe (for port 22) - "Getting Some tools together" FTPBounce.exe (for port 21) - "Welcome" eosDeviceScan.exe (for finding eos device) - "eOS Device Scanning" SMTPoverflow.exe (for port 25) - "Aggression must be punished" WebServerWorm.exe (for port 80) - "***Revenging Naix***", or "CSEC Invitation" SQLBufferOverflow.exe (for port 1433) - "-Shrine of Polar Star-" SQL_MemCorrupt.exe (for port 1433) - "CSEC Invitation - Congratulations" Decypher.exe (for decrypting files) - "Ghosting the Vault" DECHead.exe (for analyzing .dec files) - "Through the Spyglass" KBT_PortTest.exe (for port 104) - "Project Junebug" TraceKill.exe (for freezing traces) - "Bit -- Foundation" Sequencer.exe (for the final hacking) - "Bit -- Termination" Clock.exe (Um...just a clock app) - Read "-Finding Clock.exe-" SecurityTracer.exe(安全追踪程序) -来自 "First Contact"(第一次沟通), 或在完成游戏时的"Credit Server" (荣誉服务器)上。 SSHcrack.exe (ssh协议破解器)(适用端口 22) - "Getting Some tools together"(收集些工具) FTPBounce.exe (ftp“跳转攻击”破解器)(适用端口21) - "Welcome"(欢迎) eosDeviceScan.exe(eos设备搜寻器) (适用寻找eos设备) - "eOS Device Scanning"(搜寻eos设备) SMTPoverflow.exe(邮件过载破解器) (适用端口25) - "Aggression must be punished"(侵略者必将受惩处) WebServerWorm.exe (网络蠕虫破解器)(适用端口80) - "***Revenging Naix***"(向Naix复仇 译者:这不是一个官方给出的任务名,我没记错的话。), or "CSEC Invitation"(CSEC诚邀您到来) SQLBufferOverflow.exe (SQL内存缓冲区过载破解器)(适用端口1433) - "-Shrine of Polar Star-"(北极星圣地) SQL_MemCorrupt.exe(SQL_内存错误破解器) (for port 1433) - "CSEC Invitation - Congratulations"(CSEC邀请-祝贺!) (译者:根据另一个指南,这两个SQL破解器完全一样。) Decypher.exe (解密器)(适用解密文件) - "Ghosting the Vault"[拱顶鬼神(?)] DECHead.exe (十六进制文件头查看器/加密文件查看器?)(适用分析加密文件) - "Through the Spyglass"(通过望远镜) KBT_PortTest.exe[KBT端口测试器(其实也是破解器。)] (适用端口104) - "Project Junebug"(Junebug项目) TraceKill.exe(阻止追踪) (适用冻结追踪) - "Bit -- Foundation"(Bit-支柱) Sequencer.exe(排序器) (适用最后骇入) - "Bit -- Termination"(Bit-终局) Clock.exe (钟)(Hmm…只是个钟的软件) - Read "-Finding Clock.exe-"(敬参阅“寻找‘Clock.exe’”) For KBT_PortTest.exe, you can try this method if you don't get "Project Junebug" unlocked, or mistakenly abandoned it. Thank you, Elsarild! 对于KBT_PortTest.exe,若您没有解锁“Junebug项目”,或失误取消了这个任务,可以试试这个方法。谢谢您,Elsarild! http://steamcommunity.com/sharedfiles/filedetails/?id=500893610 Q, I can't use this command somehow!! Fuuuuuuuuuuuuuuu A, Make sure to check if you already have the necessary exe for the command, then try typing commands like below: Q,由于某种原因我没法用这命令!(根据相关法律法规和政策,该信息不予公布) A,确认您已具备所需的软件,然后根据以下范例输入命令。 译者:Hacknet的命令似乎更接近Linux。 Command Template - Example 命令 样板 - 范例 scp [the file's name] - scp index.html connect [the IP address] - connect 103.33.8.643 cd [the folder path] - cd /log replace [the file's name] "[target words]" "[your words]" - replace template.txt "[FIRST_NAME]" "John" (If you use "cat" and open the file, you can use 'replace "[FIRST_NAME]" "John" ' instead. Use the full command above if you get "Assuming active flag file" error.) Decypher [the file's name] [its password] - Decypher naix_secrets.dec D1CKS DECHead [the file's name] - DECHead naix_private_photos.dec mv [target's name] [new name] - mv template.txt Boorman_John[111] scp (文件传输)[the file's name(文件名)] - scp index.html connect(连接) [the IP address(IP地址)] - connect 103.33.8.643 cd (改变目录)[the folder path(文件地址)] - cd /log replace(替换) [the file's name(文件名)] "[target words(文件中目标文字)]" "[your words(你想要替代它的文字)]" - replace template.txt "[FIRST_NAME]" "John" [若您使用cat打开文件,你可以使用以下命令:“replace "[FIRST_NAME]" "John"”,若得到"Assuming active flag file"(译者:我对这句实在没辙……抱歉……)错误则打全整条命令。] Decypher [the file's name(文件名)] [its password(其密码,有时没有)] - Decypher naix_secrets.dec D1CKS DECHead [the file's name] - DECHead naix_private_photos.dec mv(移动) [target's name(目标文件名)] [new name(新名)] - mv template.txt Boorman_John[111] First Missions 终极之开始 First Contact 1, Connect to your main PC. 2, Delete or rename "SecurityTracer.exe". 3, Reply to Bit. Getting Some tools together 1, Hack "Viper-Battlestation". 2, Download "SSHcrack.exe" at /bin. 3, Reply to Bit. Maiden Flight 1, Hack "Bitwise Test PC". 2, Reply to Bit. Something in return 1, Hack "P.Anderson's Bedroom PC". 2, Go to /log, and delete all logs there. 3, Reply to Bit. First Contact 1, 连接你的主电脑(按那个绿点). 2, 删除 或重命名"SecurityTracer.exe". 3, 回复 Bit. Getting Some tools together 1, 入侵 "Viper-Battlestation". 2, 下载 "SSHcrack.exe" 在 /bin. 3, 回复 Bit. Maiden Flight 1, 入侵 "Bitwise Test PC". 2, 回复 Bit. Something in return 1, 入侵 "P.Anderson's Bedroom PC". 2, 进入/log, 并删除 all logs there. 3, 回复 Bit. Entropy Missions Entropy任务 Where to from here 1, Run "Shell" on at least one computer. 2, Connect to "Entropy Test Server". 3, Click "overload" and bypass the proxy. 4, Hack. 5, Find "Entropy_Induction_Test" and download it. Confirmation MIssion 1, Hack "Slash-Bot News Network". 2, Go to /MsgBoard/Listings. 3, Delete "Entropy_Group_engaged_in_malicious_Hacking?" and "Suspicious_arise_over_Entropy". 4, Go to /MsgBoard, and delete or rename config.sys. Welcome 1, Log in to "Entropy Asset Server". 2, Go to /bin, and download "FTPBounce.exe". Point Clicker 1, Hack "PointClicker". 2, Go to /PointClicker/Saves. 3, Delete "Mengsk.pcsav". The famous counter-hack 1, Hack "PP Marketing Inc." 2, Go to /home/WORKSPACE 3, Delete "SECURE_MAILLIST.dec". Back to school 1, Hack "Milburg High IT Office". 2, Go to /home/MH_STUFF 3, Read "pwmemo.log" and remember the password. 4, Reply with the password. () eOS Device Scanning 1, Go to "Entropy Asset Server", and download "eosDeviceScan.exe" at /bin. 2, Hack "Jason's Powerbook Plus". 3, Run "eosDeviceScan". 4, Log in to "Jason's ePhone 4S" (username: admin password: alpine). 5, Find "jjstacks@jmail.com.act" at /eos/mail. 6, Read the file, then reply the password. () Internal investigations 1, Hack "X_C Project Tablet*01//RESEARCH". 2, Find "FlightComputers.rep" at /X. 3, Read it and find its project ID. 4, Reply with the ID. () Intimidation Tactics 1, Hack "Software Enterprises" 2, Delete "Archive_Data.zip" at /home. Dengler Solutions - Return Policy 1, Hack "Starchip Communications". 2, Delete "dengler_solutions_delivery.zip" at /home. Cleaning Operation 1, Hack "Dengler Inc". 2,Delete "banished_stallion_technologies_Internal_Archive.zip". Smash N' Grab 1, Hack "JDel Home PC". 2, Scan for the eos device. 3, Log in to "Jacob's ePhone 4" as admin. 4, Read "pass.txt" at /eos/notes. 5, Reply with the password. () Aggression must be punished 1, Go to "Entropy Asset Server", and download "SMTPoverflow.exe" at /bin. 2, Hack "Proxy_Node-04". (3 or 4 shell windows recommended) 3, Delete "Macrosoft_Internal_Raid_Archive.rar" at /home. (DON'T delete logs on your main pc yet!! You'll need them later!!) ******After you get hacked by Naix, follow the steps in "Naix Missions"!!***** Hopefully that will do 1, Hack "KyonBox". 2, Read "Macrosoft_dox.txt" at /home/loot. 3, Reply with the IP address. Where to from here 1, 在至少一个服务器上启动"Shell". 2, 连接"Entropy Test Server". 3, 点击 "overload" and bypass the proxy. 4, 入侵. 5, 寻找 "Entropy_Induction_Test" 并 下载它. Confirmation MIssion 1, 入侵 "Slash-Bot News Network". 2, 进入/MsgBoard/Listings. 3, 删除 "Entropy_Group_engaged_in_malicious_Hacking?" 和"Suspicious_arise_over_Entropy". 4, 进入/MsgBoard, and 删除或重命名config.sys. Welcome 1, 登入to "Entropy Asset Server". 2, 进入/bin, 并下载 "FTPBounce.exe". Point 点击er 1, 入侵 "PointClicker". 2, 进入/PointClicker/Saves. 3, 删除 "Mengsk.pcsav". The famous counter-Hack 1, 入侵 "PP Marketing Inc." 2, 进入/home/WORKSPACE 3, 删除 "SECURE_MAILLIST.dec". Back to school 1, 入侵 "Milburg High IT Office". 2, 进入/home/MH_STUFF 3, 读 "pwmemo.log" 并记住密码. 4, 回复密码. eOS Device Scanning 1, 进入"Entropy Asset Server", 并 下载 "eosDeviceScan.exe" 在 /bin. 2, 入侵 "Jason's Powerbook Plus". 3, 启动"eosDeviceScan". 4, 登入 "Jason's ePhone 4S" (username: admin password: alpine). 5, 寻找 "jjstacks@jmail.com.act" 在 /eos/mail. 6, 读文件并回复密码. Internal investigations 1, 入侵 "X_C Project Tablet*01//RESEARCH". 2, 寻找 "FlightComputers.rep" 在 /X. 3, 阅读之并寻找project ID(项目ID). 4, 回复ID. Intimidation Tactics 1, 入侵 "Software Enterprises" 2, 删除 "Archive_Data.zip" 在 /home. Dengler Solutions - Return Policy 1, 入侵 "Starchip Communications". 2, 删除 "dengler_solutions_delivery.zip" 在 /home. Cleaning Operation 1, 入侵 "Dengler Inc". 2,删除 "banished_stallion_technologies_Internal_Archive.zip". Smash N' Grab 1, 入侵 "JDel Home PC". 2, 搜索eos设备. 3, 登入 "Jacob's ePhone 4" as admin. 4, 读 "pass.txt" 在/eos/notes. 5, 回复密码. Aggression must be punished 1, 进入"Entropy Asset Server", 下载 "SMTPoverflow.exe" 在 /bin. 2, 入侵 "Proxy_Node-04". (推荐3 到4 shell ) 3, 删除 "Macrosoft_Internal_Raid_Archive.rar" 在 /home. (***不要***删除你电脑上的记录!您还需要它!!) ******你被Naix入侵后严格遵循Naix任务中的步骤!!***** Hopefully that will do 1, 入侵 "KyonBox". 2, 读"Macrosoft_dox.txt" 在 /home/loot. 3回复IP. Naix Missions Naix任务 ***After you get hacked by Naix*** Your UX system is destroyed by Naix. Now you need to get a working "x-server.sys" using only commands. This time you'll get one from a Naix's proxy server with the commands below. 1, "cd /log" 2, "ls" 3, Now you should see the IP address which was used by Naix. 4, "connect [the IP address]" 5, "probe" 6, "SSHcrack 22" 7, "PortHack" 8, "cd /sys" 9, "scp x-server.sys" 10, "dc" 11, "reboot -i" You can choose to either go back to Entropy missions, or revenge Naix now. ***Revenging Naix*** 1, Connect to "Proxy_Node-x22" (the one in which you found the x-server.sys). 2, Scan network. 3, Hack "Naix Root Gateway". 4, Download "WebServerWorm.exe" at /bin. 5, Delete "x-server.sys" at /sys. 6, You should get an email from Naix. *You can get your original "x-server.sys" at /home if you want. gg wp 1, Hack "Nortron Security Web Server". 2, Open "index.html" at /web. 3, Replace "Nortron Security Services" with "♥♥♥♥♥". (use this command:) Hilarious 1, Connect to "Norton Security Web Server", then scan network. 2, Hack "Nortron Internal Services Server". 3, Open "REMINDER.txt" at /staff_folders/J.Abrams 4, Remember the username and password. () 5, Scan network. 6, Connect to "Nortron Mail Server", log in as J.Abrams. 7, Read "RE: Can't Log In", and remember the password for the firewall. () 8, Hack "Nortron Mainframe". (Make sure to solve the firewall with the password first!) 9, Just delete logs and disconnect. 10, Reply to the email. An Important Link Now you're given an access to "/el Message Board". Read the threads carefully and solve some myths there. 译者注: 还有一种办法可以避免Naix成功入侵你的电脑。 在被入侵的时候,打开你的shell,并按上面的trap,然后是trigger。你的电脑会像重启过一番,同时入侵会结束。这是trap唯一的用处。在未来的多人模式中,这会十分有用。 ***你被Naix入侵后*** 您的 UX系统被Naix入侵了,现在你要从Naix的服务器上获取一个正常“x-server.sys”. (译者:有些人反映之后自己界面变绿了。是的,每个x-server都有自己特殊的主题风格。) 1, "cd /log" 2, "ls" 3, 你现在应该看到Naix使用的IP. 4, "connect [the IP address]" 5, "probe" 6, "SSHcrack 22" 7, "PortHack" 8, "cd /sys" 9, "scp x-server.sys" 10, "dc" 11, "reboot -i" 现在你既可返回Entropy任务,也可向Naix复仇. ***向Naix复仇*** 1, 连接"Proxy_Node-x22" (您找到“x-server”的地方). 2, 扫描网络. 3, 入侵 "Naix Root Gateway". 4, 下载 "WebServerWorm.exe" 在/bin. 5, 删除 "x-server.sys" 在/sys. 6, 您会受到Naix的邮件. *你需要的话可以找回原来的"x-server.sys" ,它在 /home . 译者注: 很多人在这个分支上犯难,抱怨无法进入这个分支。请参考下面我过去写的一段说明文字。 “请注意Naix主电脑上的这两个文件。 1.Macrosoft_Internal_Raid_Archive.rar 2.x-server.sys 删除的文件不同,剧情也会不同。如果删除1,您会结束Naix任务,接着迅速进入CSEC。如果删除2,你就会得到Naix的邮件,接着开始/el任务。 这两个分支互斥。一旦你决定删除其中的一个文件,另一段剧情将无法开始。(应该如此。)” gg wp 1, 入侵 "Nortron Security Web Server". 2, 打开 "index.html" at /web. 3, 将 "Nortron Security Services" 替换为 "♥♥♥♥♥". Hilarious 1, 连接"Norton Security Web Server", 之后扫描网络. 2, 入侵 "Nortron Internal Services Server". 3, 打开 "REMINDER.txt" 在/staff_folders/J.Abrams 4, 记住 username 和 password. () 5, 扫描网络. 6, 连接"Nortron Mail Server", 以J.Abrams身份登录. 7, 读 "RE: Can't Log In", 并记住防火墙密码. 8, 入侵 "Nortron Mainframe". (别忘了先用密码破解firewall!) 9, 删除log并离开. 10, 回复邮件. An Important Link 你现在已经得到“/el Message Board”通行许可,阅读那里的威胁并破除那里怪事 /el Missions /el任务 You must finish all Naix's missions to access /el's message board! You won't get any emails for these /el missions, but you still need to work on them to keep the story going. Read the threads on "/el Message Board" carefully. -Shrine of the Polar Star- 1, Read the first thread about "Shrine of the Polar Star". 2, Find the IP address for "Shrine of the Polar Star", then hack it. 3, Open "index.html" at /web. 4, Find 4 IP addresses for the Trials. 5, Hack all of them one by one and get 4 reward txt files. Details for each Trials below. Polar Star - Trial of Patience 1, Hack "Polar Star - Trial of Patience". (It takes time to bypass its proxy) 2, Download "Reward_of_Patience.txt" at /home, remember the number. Polar Star - Trial of Haste 1, Hack "Polar Star - Trial of Haste". 2, Download "Reward of Haste.txt" at /home, remember the number. Polar Star - Trial of Diligence 1, Hack "Porlar Star - Trial of Diligence". 2, Scan network. 3, Hack "Trial of Diligence". 4, Download "Reward_of_Diligence.txt" at /home, remember the number. Polar Star - Trial of Focus 1, Hack "Polar Star - Trial of Focus". 2, Download "Reward of Focus.txt" at /home, remember the number. 6, The 4 numbers in the reward txt files are parts of an IP address. Sort them in the right order and connect to "Head of the Polar Star". (The correct IP address is ) 7, Hack "Head of the Polar Star". 8, Enjoy your gifts at /home/Gifts ;) () -Hacking /EL's Secure SecuLock Drive- **If you alreay have "SQLBufferOverflow.exe", you can skip 3 - 5 and just hack "/EL's Secure SecuLock Drive".** 1, Read the third thread about the "/EL's Secure SecuLock Drive". 2, Find 2 IP addresses there; one for "COME AT ME /EL's Secure SecuLock Drive" and another for "Stormrider" 3, Hack "stormrider", and scan for his eos device. 4, Log in to "Mica's ePhone 4S" as admin. 5, Read secu_lock_test_server.txt. () 6, Connect to "COME AT ME /EL's Secure SecuLock Drive" then log in as admin. 7, Delete DeleteMe.txt at /home. -Finding Clock.exe- You can ignore this one if you want. This would be the last thing you need to finish for Naix's "An Important Link". I didn't know how to find it, but the Lux Æterna's guide helped me alot!! If you have followed thig guide, you will need to work on CSEC's missions and find "Decypher.exe". http://steamcommunity.com/sharedfiles/filedetails/?id=498964442 An Important Link 你现在已经得到“/el Message Board”通行许可,阅读那里的威胁并破除那里怪事 /el Missions 要进/el Message Board先要完成Naix任务! 这些任务您不会得到任何邮件,但为了剧情发展您仍要做任务。仔细阅读"/el Message Board" 上面的威胁 -Shrine of the Polar Star- 1, 阅读"Shrine of the Polar Star"的威胁. 2, 寻找 "Shrine of the Polar Star"的IP, 入侵之. 3, 打开 "index.html" 在 /web. 4, 寻找 4 IP addresses for the Trials. 5, 入侵四个服务器,以下为指南。 Polar Star - Trial of Patience 1, 入侵 "Polar Star - Trial of Patience". (破解proxy要点时间。) 2, 下载 "Reward_of_Patience.txt" 在 /home, 记住其中的数字. Polar Star - Trial of Haste 1, 入侵 "Polar Star - Trial of Haste". 2, 下载 "Reward of Haste.txt" 在 /home, 记住其中数字. Polar Star - Trial of Diligence 1, 入侵 "Porlar Star - Trial of Diligence". 2, 扫描网络. 3, 入侵 "Trial of Diligence". 4, 下载 "Reward_of_Diligence.txt" 在 /home, 记住其中数字. Polar Star - Trial of Focus 1, 入侵 "Polar Star - Trial of Focus". 2, 下载 "Reward of Focus.txt" 在 /home, 记住其中数字. 6, 四个数字是IP的一部分,以正确的顺序组合后, 连接"Head of the Polar Star". 7, 入侵 "Head of the Polar Star". 8, 享受您的礼物!( 在 /home/Gifts ) -入侵ing /EL's Secure SecuLock Drive- **若您已有 "SQLBufferOverflow.exe", 您可跳过3 - 5 ,只需入侵 "/EL's Secure SecuLock Drive".** 1, 阅读第三个威胁: "/EL's Secure SecuLock Drive". 2, 寻找 两个IP ; 一个是"COME AT ME /EL's Secure SecuLock Drive" ,另一个是"Stormrider" 3, 入侵 "stormrider", 扫描eos设备。 4, 登入"Mica's ePhone 4S" . 5, 读secu_lock_test_server.txt. 6, 连接"COME AT ME /EL's Secure SecuLock Drive" 登入. 7, 删除Me.txt 在 /home. -寻找 Clock.exe- 你可以忽略它. 这是你完成Naix'"An Important Link"的最后一部分. 敬参阅以下指南。 http://steamcommunity.com/sharedfiles/filedetails/?id=498964442 CSEC Missions CSEC任务(原文) CSEC Invitation 1, Hack "CSEC Invitation Gauntlet". 2, Read "CONTINUE.txt" at /home/Test. 3, Scan network. 4, Hack "CSEC Gauntlet 02". 5, Read "CONTINUE.txt" at /home/Test. 6, Hack "CSEC Gauntlet 03". 7, Download "WebServerWorm.exe" at /home/Gift. 8, Read "Invitation_Passwords" at /home/Test. Remember the password. 9, Reply with the password. CSEC Invitation - Affirmation 1, Hack "www.cfc.com". 2, Scan network. 3, Hack "CFC Corporate Mainframe". 4, Read "11_Secret_Herbs_And_Spices.txt" at /home/training_files. 5, Scan network 6, Hack "CFC Records Repository". 7, Download "Seasoning_Order_Placement_Template_Pt1.docx" and "Seasoning_Order_Placement_Template_Pt2,docx". 8, Upload the 2 files to "CSEC Public File Drop". CSEC Invitation - Attenuation (This is what you get if you finished /el missions) 1, Hack "www.cfc.com". 2, Scan network. 3, Hack "CFC Corporate Mainframe". 4, Read "11_Secret_Herbs_And_Spices.txt" at /home/training_files. 5, Scan network 6, Hack "CFC Records Repository". 7, Download "Seasoning_Order_Placement_Template_Pt1.docx" and "Seasoning_Order_Placement_Template_Pt2,docx". 8, Upload the 2 files to "CSEC Public File Drop". CSEC Invitation - Congratulations 1, Log in to "CSEC Assets Server" as admin. 2, Download "SQL_MemCorrupt.exe" at /bin/SQL_Mem_Corrupter (you don't need this if you already have "SQLBufferOverflow.exe") and "Sequencer.exe" at /bin/Sequencer. 3, Now it's time for CSEC missions.... Rod of Asclepius 1, Hack "Universal Medical". 2, Search for "Jonas Sandburg". 3, Click "e-mail this record", and send the record to "gila@jmail.com". Binary Universe(ity) 1, Hack "International Academic Databse". 2, Search for "John Stalvern". 3, Click "Add Degree". 4, Add the following information: "Manchester Univeristy" "Masters in Digital Security" "3.1" 5, Click "Save and Return". 6, Delete logs!! Ghosting the Vault 1, Hack "CSEC Crossroads Server". 2, Download "encrypt_source.dec" at /home. 3, Hack "DEC Solutions Web Server". 4, Scan network. 5, Hack "DEC Solutions Mainframe". 6, Download "Decypher.exe" at /Staff/A.Carey. 7, Connect to your main PC, then go to /home. 8, Decrypt "encrypt_source.dec". (Use this command:) 9, Upload "encrypt_source.cs" to CSEC Public File Drop". Imposters on Death Row 1, Hack "Death Row Records Database". 2, Go to /dr_database/records. 3, Remove Joseph Felman's record. (Use this command:) Bit's disappearance Investigation 1, Hack "Bitwise Relay 01". 2, Read Home_Base.txt at /home. 3, Connect to "Bitwise Drop Server", and hack it. 4, Download "READ_all_hackers.txt" at /Drop/Uploads. 5, Upload "READ_all_hackers.txt" to "CSEC Public File Drop". Through the Spyglass 1, Hack "Joseph Scott's Battlestation". 2, Download "DECHead.exe" at /home/work. 3, You'll get a new email once you realy, now connect to "CSEC Crossroads Server". 4, Download "CSEC_encode_1.dec" at /home. 5, Connect to your main PC, then analyze "CSEC_encode_1.dec" with "DECHead.exe". (Use this command:) 6, You'll find an IP address for "Macrosoft Workhorse". Connect to it and hack it. 7, Read "3345633.log" at /WORKLOGS, the password is there. Red Line You don't need to hack this server completely! Just attempting to hack it is enough! 1, Connect to "CCC Hacksquad Filedump". 2, As soon as you start hacking, you will enter "emergency recovery mode". Now you should change your IP address quickly. 3, Connect to "ISP Management System". (Use this command:) 4, Hack "ISP Management System". 5, Click "Search for IP", then type your current IP address. (It should be shown at bottm-left corner.) 6, Click "Assign New IP", your PC will restart immediately. 7, Reply the email. Some tips for hacking this one completely: *EASIEST WAY to beat it: Just keep hacking the server even if you enter the emergency recovery mode. Each command will reset the warning message and you will be able to finish hacking. * If you want to download the files in this server, you can do it while emergency recovery mode. You'll need to type commands really quickly though..... Wipe the record clean 1, Hack "International Academic Detabase", or just log in as admin if you've done this before. 2, Search for "Jacob Stevens". 3, Click "Delete", then "Confirm". 4, Delete logs before you disconnect! Jailbreak 1, Hack "Sal_Home_Workstation". 2, Scan for his eos device. 3, Log in to "Elanor Helleran's ePhone 4s" as admin. 4, Read "ids.txt" at /eos/notes, and remember the registration ID. 5, Reply with the registration ID. A Convincing Application 1, Log in to "CSEC Crossroads Server" as admin. 2, Download "FOF_Screenplay.doc" at /home. 3, Analyze "T2_Screenplay.dec" with "DECHead.exe". You'll get an IP address. 4, Hack "Jason's LackBook Pro". 5, Go to /home/scripts, and upload "FOF_Screenplay.doc" from your PC. Unjust Absence 1, Log in to "CSEC Assets Server" as admin. 2, Download "template.txt" at /home/Templates/DeathRowDatabaseTemplate. 3, Connect to your main PC, and open "template.txt" at /home. 4, Edit "template.txt". Use these commands: 5, Rename "template.txt" to . 6, Connect to "Death Row Records Database", and hack it or log in as admin if you have already hacked it. 7, Go to /dr_database/records, and upload the file, . Two Ships in the night 1, Connect to "CSEC Crossroads Server", and find "C_EXE_contact.dec" at /home. 2, Decrypt "C_EXE_contract.dec" with "Decypher.exe". (Use this command:) 3, Download "C_EXE_contact.txt". () 4, Upload "C_EXE_contact.txt" to "CSEC Public File Drop". Project Junebug 1, Hack "Universal Medical". 2, Search for "Elliot Whit". 3, Send his record to your email address. (Click "e-email this record" then "Specify Address".) 4, Go to your Jmail inbox, and read Elliot's record. You will find 2 IP addresses here. 5, Connect to "Kellis Biotech Client Services", and hack it. 6, Optional, but necessary if you wanna know what you're doing: Read all news on "Kellis Biotech News". 7, Scan network 8, Hack "Kellis Biotech Prodection Asset Server". 9, Download "KBT_PortTest.exe" at /home/Production/Output. This software will allow you to hack port 104. 10, Now go back to "kellis Biotech Client Services", and read "#0E0015_-_Pacemaker_v2.44_Firmware_and Patching" at /MsgBoard/listings. You'll find an IP address here. 11, Connect to "Eidolon Soft Production Server", and hack it. 12, Read "Eidolon_Security_Notes.txt" at /projects/Internal. Remember the user name and the password. 13, Download "PacemakerFirmware_Cycle_Test.dll" at /projects/KellisBT/Tests. 14, Connect to "KBT-PM 2.44 REG#10811", and hack it. 15, Go to /KBT_Pacemaker, and upload "PacemakerFirmware_Cycle_Test.dll" there. 16, Click "View Monitor". 17, Log in as EAdmin. () 18, Click "Administrate Firmware". 19, Choose "PacemakerFirmware_Cycle_Test.dll", then click "Activate This Firmware". 20, Now watch his heart beat.... 21, RIP CSEC Missions CSEC任务(译文) CSEC Invitation 1, 入侵 "CSEC Invitation Gauntlet". 2, 读 "CONTINUE.txt" 在 /home/Test. 3, 扫描网络. 4, 入侵 "CSEC Gauntlet 02". 5, 读"CONTINUE.txt" 在 /home/Test. 6, 入侵 "CSEC Gauntlet 03". 7, 下载 "WebServerWorm.exe" 在 /home/Gift. 8, 读 "Invitation_Passwords" 在 /home/Test.记住密码. 9, 回复密码. CSEC Invitation - Affirmation 1, 入侵 "www.cfc.com". 2, 扫描网络. 3, 入侵 "CFC Corporate Mainframe". 4, 读 "11_Secret_Herbs_And_Spices.txt" 在 /home/training_files. 5, 扫描网络 6, 入侵 "CFC Records Repository". 7, 下载 "Seasoning_Order_Placement_Template_Pt1.docx" and "Seasoning_Order_Placement_Template_Pt2,docx". 8, 上传文件到 "CSEC Public File Drop". CSEC Invitation - Attenuation (This is what you get if you finished /el missions) 1, 入侵 "www.cfc.com". 2, 扫描网络. 3, 入侵 "CFC Corporate Mainframe". 4, Read "11_Secret_Herbs_And_Spices.txt" 在 /home/training_files. 5, 扫描网络 6, 入侵 "CFC Records Repository". 7, 下载 "Seasoning_Order_Placement_Template_Pt1.docx" and "Seasoning_Order_Placement_Template_Pt2,docx". 8, Upload the 2 files to "CSEC Public File Drop". (译者:我实在不清楚上面两个任务有何区别——它们似乎完全一样。) CSEC Invitation - Congratulations 1, 登入to "CSEC Assets Server" as admin. 2, 下载 "SQL_MemCorrupt.exe" 在/bin/SQL_Mem_Corrupter (有了 "SQLBufferOverflow.exe"您就不需要这个了。) 及"Sequencer.exe" 在/bin/Sequencer. 终于进入CSEC任务了…... Rod of Asclepius 1, 入侵 "Universal Medical". 2, 寻找"Jonas Sandburg". 3, 点击 "e-mail this record", 发到"gila@jmail.com". Binary Universe(ity) 1, 入侵 "International Academic Databse". 2, 寻找"John Stalvern". 3, 点击 "Add Degree". 4, 增加以下记录(译者:用replace命令吧): "Manchester Univeristy" "Masters in Digital Security" "3.1" 5, 点击 "Save and Return". 6, 删除 logs!!(译者:说实话,我实在不知道不删log会怎么样。) 译者:这是不是对uplink致敬呢? Ghosting the Vault 1, 入侵 "CSEC Crossroads Server". 2, 下载 "encrypt_source.dec" 在 /home. 3, 入侵 "DEC Solutions Web Server". 4, 扫描网络. 5, 入侵 "DEC Solutions Mainframe". 6, 下载 "Decypher.exe" at /Staff/A.Carey. 7, 连接你的主电脑, 进入/home. 8, 解密 "encrypt_source.dec". 9, 上传"encrypt_source.cs" 到CSEC Public File Drop". Imposters on Death Row 1, 入侵 "Death Row Records Database". 2, 进入/dr_database/records. 3, 删除 Joseph Felman 记录. Bit's disappearance Investigation 1, 入侵 "Bitwise Relay 01". 2, 读 Home_Base.txt 在 /home. 3, 连接"Bitwise Drop Server", 入侵它 . 4, 下载 "READ_all_Hackers.txt" 在 /Drop/Uploads. 5, 上传"READ_all_Hackers.txt" 到 "CSEC Public File Drop". Through the Spyglass 1, 入侵 "Joseph Scott's Battlestation". 2, 下载 "DECHead.exe" 在 /home/work. 3, 你会得到一个邮件, 连接"CSEC Crossroads Server". 4, 下载 "CSEC_encode_1.dec" 在 /home. 5, 连接主电脑, 侦听"CSEC_encode_1.dec" 用 "DECHead.exe". 6, You'll 寻找 an IP address for "Macrosoft Workhorse". 连接并入侵它. 7, 读"3345633.log" 在 /WORKLOGS, 密码在那. Red Line 不用完全入侵这服务器! 假装试着入侵即可! 1, 连接"CCC Hacksquad Filedump". 2, 您一开始入侵, 就会进入"emergency recovery mode". 您要快点改IP. 3, 连接"ISP Management System". (译者:在右下角,应该是第一行.) 4, 入侵 "ISP Management System". 5, 点击 "Search for IP", 输入您的电脑IP. (其应在右下角.) 6, 点击 "Assign New IP", 您的电脑会立即重启. 7, 回复邮件. 完全入侵之的小帮助: *入侵它的最容易的办法:即使进入"emergency recovery mode"仍入侵这个服务器. 每个命令都会重新设定倒计时,使您最终完成入侵。 (译者:入侵成功后您会找到一个新x—server,对于我来说,如此漂亮的界面让我感觉值了。) * 若您想下载服务器的文件, 您可以在emergency recovery mode做到这一点. 虽然您的手速一定要快..... Wipe the record clean 1, 入侵或登录 "International Academic Detabase". 2, 搜索 "Jacob Stevens". 3, 点击 "Delete", then "Confirm". 4, 删除记录! Jailbreak 1, 入侵 "Sal_Home_Workstation". 2, 搜索eos设备. 3, 登入 "Elanor Helleran's ePhone 4s" . 4, 读 "ids.txt" 在/eos/notes, 记住登入ID. 5, 回复 ID. A Convincing Application 1, 登入 "CSEC Crossroads Server" . 2, 下载 "FOF_Screenplay.doc" 在 /home. 3, 分析 "T2_Screenplay.dec" 用 "DECHead.exe". 你会得到ip地址. 4, 入侵 "Jason's LackBook Pro". 5, 进入/home/scripts, 并上传 "FOF_Screenplay.doc" . Unjust Absence 1, 登入to "CSEC Assets Server" . 2, 下载 "template.txt" 在 /home/Templates/DeathRowDatabaseTemplate. 3, 连接your main PC, 打开"template.txt" 在 /home. 4, 编辑"template.txt". 5, 重命名 "template.txt" . 6, 连接"Death Row Records Database", 入侵或登入之. 7, 进入/dr_database/records, 上传文件 . Two Ships in the night 1, 连接"CSEC Crossroads Server", 寻找 "C_EXE_contact.dec" 在 /home. 2, 解密 "C_EXE_contract.dec" 用"Decypher.exe". 3, 下载 "C_EXE_contact.txt". 4, 上传 "C_EXE_contact.txt" 到 "CSEC Public File Drop". Project Junebug 译者广告:您也可以参考我的攻略http://tieba.baidu.com/p/4456967644?lp=5028&mo_device=1&is_jingpost=1&pn=0& 1, 入侵 "Universal Medical". 2, 搜索"Elliot Whit". 3, 把这个记录发到你邮箱上. (点击 "e-email this record" 然后"Specify Address".) 4, 进入您的邮箱. 您会在此找到两个IP. 5, 连接"Kellis Biotech Client Services", 入侵它. *6, 可选,但是如果要搞明白自己在干什么最好读"Kellis Biotech News"的所有文章. 7, 扫描网络 8, 入侵 "Kellis Biotech Prodection Asset Server". 9, 下载 "KBT_PortTest.exe" 在 /home/Production/Output. 这软件可让您入侵 端口104. 10, 回到 "kellis Biotech Client Services", 读"#0E0015_-_Pacemaker_v2.44_Firmware_and Patching" at /MsgBoard/listings.您会找到IP. 11, 连接"Eidolon Soft Production Server", 入侵它. 12, 读 "Eidolon_Security_Notes.txt" at /projects/Internal.记住用户名、密码. 13, 下载 "PacemakerFirmware_Cycle_Test.dll" 在/projects/KellisBT/Tests. 14, 连接"KBT-PM 2.44 REG#10811", 入侵它. 15, 进入/KBT_Pacemaker, 上传 "PacemakerFirmware_Cycle_Test.dll" . 16, 点击 "View Monitor". 17, 以EAdmin登入. 18, 点击 "Administrate Firmware". 19, 选择 "PacemakerFirmware_Cycle_Test.dll", 点击 "Activate This Firmware". 20, 默默注视他(?)的心电图... 21, 安息吧. Final Missions 终极之终极 Bit -- Foundation 1, Connect to "CSEC Assets Server". 2, Decrypt "Tracekill.dec" at /bin/TK. (Use this command:) 3, Download "Tracekill.exe". Bit -- Substantiation 1, Connect to "Bitwise Repo Base", and hack it. 2, Analyze "hn_repo_archieve.dec" with "DECHead.exe". You'll get an IP address. 3, Send the IP address to V. Bit -- Investigation ***Use "Tracekill.exe" wisely!!*** 1, Hack "EnTech Web Server". 2, Scan network. 3, Hack "EnWorkstationCore". 4, Scan network. 5, Hack "EnTech Workstation_008". 6, Download "Prometheus.txt" at /WORKSTATION/store. You'll need the password in it later. 7, Download "StoreServIPs.txt" at /WORKSTATION/store. You'll find 2 IP addresses in it. 8, Go to "En_Prometheus", then log in as admin. (usename:password:) 9, You'll get an email from V. Bit -- Propagation 1, Go back to "En_Prometheus", then log in as admin. 2, Scan for eos devices. 3, Connect to "ENTECH_TEST_01's ePHONE 4S". 4, Read "nstanford@entech.com.act" at /eos/mail. Remember the username and the password. 5, Connect to "EnTech Mail Server", then log in as nstanford@entech.com. (username:password:) 6, Read the email titled "Re"Romulus passwd". Remember the password. 7, Connect to En_Romulus, then log in as admin. (username:password: 8, Read "Contractor_Server.doc" at /STORE/Contractors. This is the admin password for "EnTech External Contractor Relay Server".. 9, Send the password to V. Bit -- Vindication 1, Connect to "EnTech External Contractor Relay Server". 2, Download "heart.dec" at /Contractors/Bit. 3, Connect to your main PC, then decrypt "heart.dec". (Use this command:) 4, Read "heart.txt". 5, Reply to V. Bit -- Termination 1, If you don't have "Sequencer.exe" yet, connect to "CSEC Assets Server", and download it at /bin/Sequencer. 2, Run "Shell" on your main PC and some other computers. 3 or 4 recommended. 3, Start "Sequencer.exe" and click "ACTIVATE" 8, Hack "EnTech_offline_Cycling_Backup"!!! GO GO GO!!! 9, Delete all files in /ARCHIVE/Hacknet/24-02, /ARCHIVE/Hacknet/03-12, /ARCHIVE/Hacknet/18-09. 10, Delete logs. 11, Disconnect..... 12, Reply to V. Terminal 1, Connect to "PortHack.Heart. 2, Hack "PortHack.Heart".......!? Bit -- Foundation 1, 连接"CSEC Assets Server". 2,解密"Tracekill.dec" 在 /bin/TK. 3, 下载 "Tracekill.exe". Bit -- Substantiation 1, 连接"Bitwise Repo Base", 入侵它. 2, 分析"hn_repo_archieve.dec" 用 "DECHead.exe". 您会得到一个IP. 3, 把IP发给 V. Bit -- Investigation ***善用 "Tracekill.exe" !!*** (译者:Entech大部分服务器都无法正常破解,注意。) 1, 入侵 "EnTech Web Server". 2, 扫描网络. 3, 入侵 "EnWorkstationCore". 4, 扫描网络. 5, 入侵 "EnTech Workstation_008". 6, 下载 "Prometheus.txt" 在/WORKSTATION/store. 您会稍候需要其中的密码. 7, 下载 "StoreServIPs.txt" 在 /WORKSTATION/store. 您要找两个IP. 8, 进入"En_Prometheus", 登入. 9, 您会得到V的邮件. Bit -- Propagation 1, 回到 "En_Prometheus", 登入. 2, 扫描eos设备. 3, 连接"ENTECH_TEST_01's ePHONE 4S". 4, 读 "nstanford@entech.com.act" 在/eos/mail. 记住其中的用户名、密码. 5, 连接"EnTech Mail Server", 以 nstanford登入. (2016/10/21注:邮箱服务器是不需要后面的@的,很抱歉造成误导。) 6, 阅读标题为 "Re:Romulus passwd"的邮件. 记住密码. 7, 连接En_Romulus, 登入. 8, 读 "Contractor_Server.doc" 在/STORE/Contractors. "EnTech External Contractor Relay Server"的密码就在里面. 9, 发送密码给 V. Bit -- Vindication 1, 连接"EnTech External Contractor Relay Server". 2, 下载 "heart.dec" 在 /Contractors/Bit. 3, 连接your main PC, then decrypt "heart.dec". 4, 读"heart.txt". 5, 回复 V. Bit -- Termination 1, 若您没有 "Sequencer.exe" , 连接"CSEC Assets Server", 下载它在 /bin/Sequencer. 2, 启动"Shell" 在您的电脑及其它几个电脑.3-4个够了。 3, 启动 "Sequencer.exe" 点击 "ACTIVATE" 8, 入侵 "EnTech_offline_Cycling_Backup"!!!快点!!! 9, 删除 /ARCHIVE/Hacknet/24-02, /ARCHIVE/Hacknet/03-12, /ARCHIVE/Hacknet/18-09的所有文件. 10, 删除记录. (译者:您事实上可以下载上面的文件,但您很快会发现其中Hacknet.exe文件无法运行。您明白为什么吗? Sequencer还能再运行一次以破解服务器。) 11, 断线..... 12, 回复 V. Terminal 1, 连接"PortHack.Heart. 2, 入侵 "PortHack.Heart".......!? Final Words from Me 最后 Final Words from Me Thank you for reading my guide. I hope my guide helped you! Anyway, if you have followed this guide too much, I recommend you to play a new session after you see the ending. Hacknet's story is pretty good and interesting, you would be pleased when you understand what was going on with those hackers, and see the ending again :D 最后 感谢阅读我的指南。我希望我的指南帮到你!无论如何,若您一直顺着指南走,我推荐您在开个存档玩。Hacknet故事很好,若您明白究竟发生些什么,你会很高兴的。:D Thank you again, 再次感谢 Gorimaccha(作者) 译者记 非常,非常抱歉。
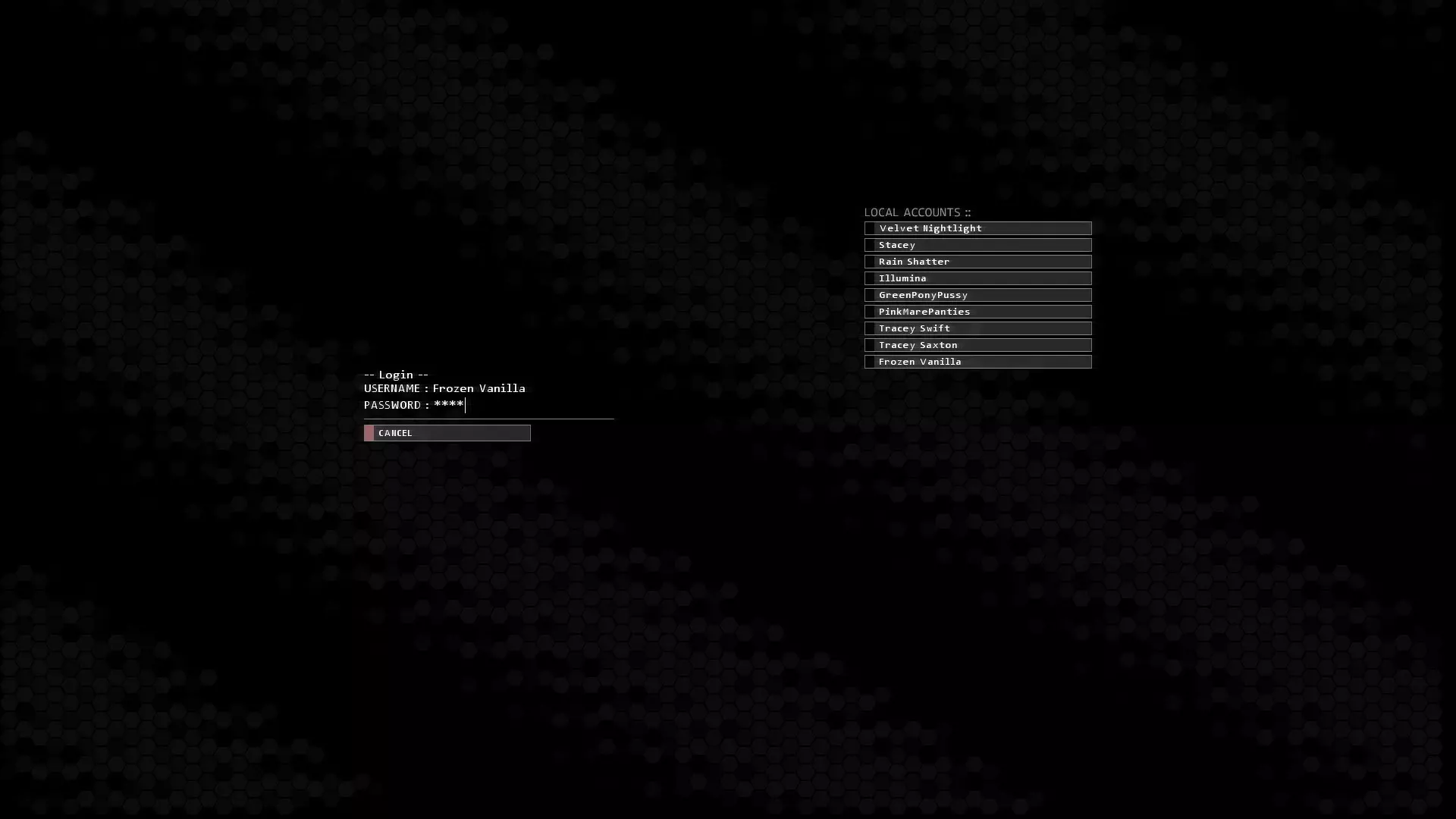
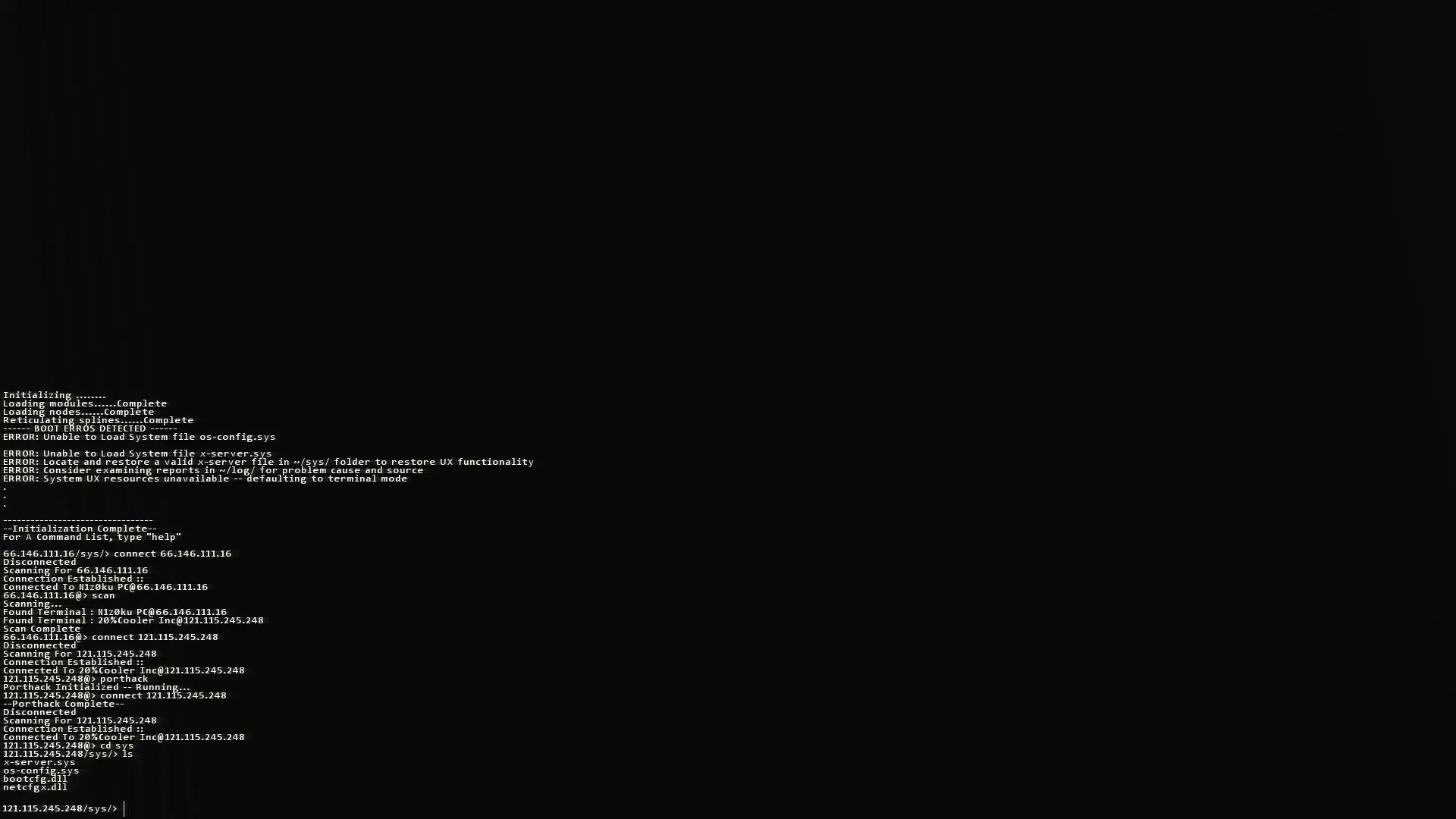
在你删除Naix窃取的Macrosoft文件后,他删除了你的x-server.sys文件。 以下是你恢复系统所需的代码。 第一部分:连接Naix的代理服务器 重启后,你只剩下命令提示符。这是因为另一名名为Naix的黑客删除了你的x-server.sys文件。 现在你需要获取另一个x-server.sys文件。操作方法如下: 首先使用cd log命令进入/log目录。在此处输入ls。 在其中一个日志中,你会找到黑客的IP地址。查看日志名称,你会发现Naix删除x-server.sys文件后留下的日志。记下这个IP地址,因为你会用到它。 现在,在命令提示符中输入connect [此处填入Naix的IP地址]。你将连接到他的代理服务器。 输入probe查看可用端口列表。你会发现代理已消失,大部分端口也已关闭。输入SSHCrack 22破解端口,然后使用porthack进入。现在你已连接成功。 第二部分:获取x-server.sys文件 从这里开始就很简单了。 只需使用cd sys命令进入他的/sys目录。输入ls查看该目录下的文件列表。如果看到x-server.sys文件,输入scp x-server.sys即可下载该文件。它会立即保存到正确的目录中。 现在连接回你自己的IP。如果你不知道自己的IP地址,先输入cd ..,然后输入cd log,再输入ls。下载了x-server.sys文件的那个IP就是你的IP地址。你可以把这个记下来或者记住,但现在只需输入connect [此处填写IP地址]。之后,输入reboot重启系统,或输入reboot -i立即重启系统。 另一种方法 另一种方法可能更简单。 首先使用scan扫描网络,查看是否有其他IP地址连接到你的网络。应该会显示一个其他IP地址,把它记下来或记住,然后使用connect [此处填写IP地址]连接到该网络。使用cd sys进入/sys目录,然后使用scp x-server.sys下载文件。之后,使用connect[此处填写IP地址]连接到你自己的网络。最后输入reboot即可完成。阻止重启 你需要快速操作,但确实可以阻止奈克斯重启你的网络。方法如下: 奈克斯关闭你的电脑前的最后一步是执行“Forkbomb”(叉形炸弹)。这是一个你也拥有的可执行文件。它会使系统内存过载,导致系统崩溃、关闭所有程序并重启。但当你看到他启动了叉形炸弹(当你看到屏幕左侧闪烁随机数字时就会发生),你需要做几件简单的事。首先输入“ps”查看网络上所有当前进程。你只需找到叉形炸弹的进程ID,然后输入“kill [此处填入进程ID]”。你仍然需要恢复你的x-server.sys文件,但至少你能恢复用户界面了。感谢Expack提供的提示 长话短说 重启后你会连接到自己的电脑。首先,前往/log目录并找到Naix的IP地址。连接到该地址并进入他的/sys文件。在那里,下载他的x-server.sys文件,然后重新连接到你自己的设备。之后,你只需重启系统,一切就会恢复正常(嗯,几乎恢复正常)。 感谢阅读! 我很快会制作最后几个任务的指南,因为很多人在那里会遇到困难。
本指南为新手玩家整理了一些建议。或许有经验的玩家也能从中发现有用的内容,因为我收集的这些要点在游戏中并未提及,或者很容易被忽略。 命令行 - 不要忘记自动补全功能(Tab键)。你可以在输入命令以及文件/目录时使用它。 - 若要执行之前输入过的命令,可以使用上下方向键来浏览历史命令。这在分析防火墙或程序因内存限制初次无法启动时非常有用。 - 你可以使用“addNote [你的备注]”命令来添加自己的备注。 - “exe”命令会显示你拥有的所有工具。优化入侵流程 如果服务器同时具有防火墙保护和代理检测功能,你可以先开始对代理检测进行过载攻击,然后在过载仍在进行时着手移除防火墙保护。 要加快代理检测的过载速度,请使用多个shell。 你可以同时运行多个端口开放工具(数量取决于你的内存容量)。 在入侵过程中,你可以随时断开连接(“dc”)以避免被追踪,且你的进度(已开放的端口和已绕过的安全措施)将会保存,你可以重新连接并继续入侵。此功能适用于大多数服务器,但也有少数服务器要求你一次性完成所有操作。 一般建议 如果你之前已成功访问过某服务器,现在需要再次访问时,无需再次强行入侵。你只需选择登录选项,就能在那里看到正确的用户名/密码组合。 如果你过于依赖图形用户界面来浏览文件系统和查看文件,可能会忘记你在图形用户界面中所做的一切实际上都是在命令行中执行的。当你需要在其他地方使用文件中的信息时(例如通过电子邮件发送),请记住这一点。无需记住或记录信息,只需在控制台中查看文件内容即可。 最后 希望你能在这里找到有用的东西。请记住:始终掩盖你的痕迹! cd /log rm *
I made this guide for those who think they're completely stuck. I don't recommend you to read this too much if you seek some challenge :) All missions available now! Basic Tips ***IMPORTANT*** Some computers/servers may have different names on them, but what you need to do should be the same. Just follow the steps, you will be fine. DON'T abandon any missions atm!! It will most likey cause serious problems and make you unable to finish the game! 1, Type commands as soon as possible. 2, Delete logs when you disconnect. 3, You need to reply almost every time you finish a mission. 4, Always use "Scan Network" option when you successfully hack a computer. 5, Don't delete/rename files unnecessarily. <-This is important!! 6, Use auto-complete for commands and file names. (Tab key) 7, Always use "admin" "alpine" to log in to any eos devices. Troubleshooting Common Problems Q, I don't get an email to start a new mission!! What do I do now!?A, Make sure to check following things: 1, Your previous mission has finished. (Click "Reply" in the email for it and see if "Mission Incomplete" message shows up.) 2, You don't have any available missions in your current faction's contracts server. (Or the message board if you're working on /el missions.) 3, Restart your game and your problem is still there. For "gg wp" from Naix, you need to revenge Naix BEFORE you start any new Entropy mission. Details in "Naix Missions" section below. If none of these helps you, you might have had a critical bug... The devs are working on an update to fix many bugs, so wait for it... Meanwhile, you still can try 2 options: 1, Editing your save data (Here's the link: http://steamcommunity.com/app/365450/discussions/0/530649887208580632/ Be super careful with your savedata.) 2, Start a new session (This is much easier... You also can work on achievements that you missed.) Q, I don't have the necessary exe file to do this mission!! UGGHHHHA, Here is the list of exe files, and in which mission you can find them. Use "CTRL+F" on this guide and search for them. SecurityTracer.exe - "First Contact", or on "Credit Server" after you finish the game. SSHcrack.exe (for port 22) - "Getting Some tools together" FTPBounce.exe (for port 21) - "Welcome" eosDeviceScan.exe (for finding eos device) - "eOS Device Scanning" SMTPoverflow.exe (for port 25) - "Aggression must be punished" WebServerWorm.exe (for port 80) - "***Revenging Naix***", or "CSEC Invitation" SQLBufferOverflow.exe (for port 1433) - "-Shrine of Polar Star-" SQL_MemCorrupt.exe (for port 1433) - "CSEC Invitation - Congratulations" Decypher.exe (for decrypting files) - "Ghosting the Vault" DECHead.exe (for analyzing .dec files) - "Through the Spyglass" KBT_PortTest.exe (for port 104) - "Project Junebug" TraceKill.exe (for freezing traces) - "Bit -- Foundation" Sequencer.exe (for the final hacking) - "Bit -- Termination" Clock.exe (Um...just a clock app) - Read "-Finding Clock.exe-" For KBT_PortTest.exe, you can try this method if you don't get "Project Junebug" unlocked, or mistakenly abandoned it. Thank you, Elsarild! http://steamcommunity.com/sharedfiles/filedetails/?id=500893610 Q, I can't use this command somehow!! FuuuuuuuuuuuuuuuA, Make sure to check if you already have the necessary exe for the command, then try typing commands like below: Command Template - Example scp [the file's name] - scp index.html connect [the IP address] - connect 103.33.8.643 cd [the folder path] - cd /log replace [the file's name] "[target words]" "[your words]" - replace template.txt "[FIRST_NAME]" "John" (If you use "cat" and open the file, you can use 'replace "[FIRST_NAME]" "John" ' instead. Use the full command above if you get "Assuming active flag file" error.) Decypher [the file's name] [its password] - Decypher naix_secrets.dec D1CKS DECHead [the file's name] - DECHead naix_private_photos.dec mv [target's name] [new name] - mv template.txt Boorman_John[111] First Missions First Contact1, Connect to your main PC. 2, Delete or rename "SecurityTracer.exe". 3, Reply to Bit. Getting Some tools together1, Hack "Viper-Battlestation". 2, Download "SSHcrack.exe" at /bin. 3, Reply to Bit. Maiden Flight1, Hack "Bitwise Test PC". 2, Reply to Bit. Something in return1, Hack "P.Anderson's Bedroom PC". 2, Go to /log, and delete all logs there. 3, Reply to Bit. Entropy Missions Where to from here1, Run "Shell" on at least one computer. 2, Connect to "Entropy Test Server". 3, Click "overload" and bypass the proxy. 4, Hack. 5, Find "Entropy_Induction_Test" and download it. Confirmation MIssion1, Hack "Slash-Bot News Network". 2, Go to /MsgBoard/Listings. 3, Delete "Entropy_Group_engaged_in_malicious_Hacking?" and "Suspicious_arise_over_Entropy". 4, Go to /MsgBoard, and delete or rename config.sys. Welcome1, Log in to "Entropy Asset Server". 2, Go to /bin, and download "FTPBounce.exe". Point Clicker1, Hack "PointClicker". 2, Go to /PointClicker/Saves. 3, Delete "Mengsk.pcsav". The famous counter-hack1, Hack "PP Marketing Inc." 2, Go to /home/WORKSPACE 3, Delete "SECURE_MAILLIST.dec". Back to school1, Hack "Milburg High IT Office". 2, Go to /home/MH_STUFF 3, Read "pwmemo.log" and remember the password. 4, Reply with the password. (*******) eOS Device Scanning1, Go to "Entropy Asset Server", and download "eosDeviceScan.exe" at /bin. 2, Hack "Jason's Powerbook Plus". 3, Run "eosDeviceScan". 4, Log in to "Jason's ePhone 4S" (username: admin password: alpine). 5, Find "jjstacks@jmail.com.act" at /eos/mail. 6, Read the file, then reply the password. (tintin7) Internal investigations1, Hack "X_C Project Tablet*01//RESEARCH". 2, Find "FlightComputers.rep" at /X. 3, Read it and find its project ID. 4, Reply with the ID. (1938) Intimidation Tactics1, Hack "Software Enterprises" 2, Delete "Archive_Data.zip" at /home. Dengler Solutions - Return Policy1, Hack "Starchip Communications". 2, Delete "dengler_solutions_delivery.zip" at /home. Cleaning Operation1, Hack "Dengler Inc". 2, Delete "banished_stallion_technologies_Internal_Archive.zip". Smash N' Grab1, Hack "JDel Home PC". 2, Scan for the eos device. 3, Log in to "Jacob's ePhone 4" as admin. 4, Read "pass.txt" at /eos/notes. 5, Reply with the password. (warsix22) Aggression must be punished1, Go to "Entropy Asset Server", and download "SMTPoverflow.exe" at /bin. 2, Hack "Proxy_Node-04". (3 or 4 shell windows recommended) 3, Delete "Macrosoft_Internal_Raid_Archive.rar" at /home. (DON'T delete logs on your main pc yet!! You'll need them later!!) ******After you get hacked by Naix, follow the steps in "Naix Missions"!!***** Hopefully that will do1, Hack "KyonBox". 2, Read "Macrosoft_dox.txt" at /home/loot. 3, Reply with the IP address. Naix Missions ***After you get hacked by Naix***Your UX system is destroyed by Naix. Now you need to get a working "x-server.sys" using only commands. This time you'll get one from a Naix's proxy server with the commands below. 1, "cd /log" 2, "ls" 3, Now you should see the IP address which was used by Naix. 4, "connect [the IP address]" 5, "probe" 6, "SSHcrack 22" 7, "PortHack" 8, "cd /sys" 9, "scp x-server.sys" 10, "dc" 11, "reboot -i" You can choose to either go back to Entropy missions, or revenge Naix now. ***Revenging Naix***1, Connect to "Proxy_Node-x22" (the one in which you found the x-server.sys). 2, Scan network. 3, Hack "Naix Root Gateway". 4, Download "WebServerWorm.exe" at /bin. 5, Delete "x-server.sys" at /sys. 6, You should get an email from Naix. *You can get your original "x-server.sys" at /home if you want. gg wp1, Hack "Nortron Security Web Server". 2, Open "index.html" at /web. 3, Replace "Nortron Security Services" with "♥♥♥♥♥". (use this command:replace index.html "Nortron Security Services" "♥♥♥♥♥") Hilarious1, Connect to "Norton Security Web Server", then scan network. 2, Hack "Nortron Internal Services Server". 3, Open "REMINDER.txt" at /staff_folders/J.Abrams 4, Remember the username and password. (username: j.abrams password: bootyking420) 5, Scan network. 6, Connect to "Nortron Mail Server", log in as J.Abrams. 7, Read "RE: Can't Log In", and remember the password for the firewall. (123456789ABC) 8, Hack "Nortron Mainframe". (Make sure to solve the firewall with the password first!) 9, Just delete logs and disconnect. 10, Reply to the email. An Important LinkNow you're given an access to "/el Message Board". Read the threads carefully and solve some myths there. /el Missions You must finish all Naix's missions to access /el's message board! You won't get any emails for these /el missions, but you still need to work on them to keep the story going. Read the threads on "/el Message Board" carefully. -Shrine of the Polar Star-1, Read the first thread about "Shrine of the Polar Star". 2, Find the IP address for "Shrine of the Polar Star", then hack it. 3, Open "index.html" at /web. 4, Find 4 IP addresses for the Trials. 5, Hack all of them one by one and get 4 reward txt files. Details for each Trials below. Polar Star - Trial of Patience 1, Hack "Polar Star - Trial of Patience". (It takes time to bypass its proxy) 2, Download "Reward_of_Patience.txt" at /home, and remember the number in it. Polar Star - Trial of Haste 1, Hack "Polar Star - Trial of Haste". 2, Download "Reward of Haste.txt" at /home, and remember the number in it. Polar Star - Trial of Diligence 1, Hack "Porlar Star - Trial of Diligence". 2, Scan network. 3, Hack "Trial of Diligence". 4, Download "Reward_of_Diligence.txt" at /home, and remember the number in it. Polar Star - Trial of Focus 1, Hack "Polar Star - Trial of Focus". 2, Download "Reward of Focus.txt" at /home, and remember the number in it. 6, The 4 numbers in the reward txt files are parts of an IP address. Sort them in the right order and connect to "Head of the Polar Star". (The correct IP address is 103.33.8.162) 7, Hack "Head of the Polar Star". 8, Enjoy your gifts at /home/Gifts ;) (Don't forget to get "SQLBufferOverflow.exe".) -Hacking /EL's Secure SecuLock Drive-**If you alreay have "SQLBufferOverflow.exe", you can skip 3 - 5 and just hack "/EL's Secure SecuLock Drive".** 1, Read the third thread about the "/EL's Secure SecuLock Drive". 2, Find 2 IP addresses there; one for "COME AT ME /EL's Secure SecuLock Drive" and another for "Stormrider" 3, Hack "stormrider", and scan for his eos device. 4, Log in to "Mica's ePhone 4S" as admin. 5, Read secu_lock_test_server.txt. (ithoughtyouweremakingtea - That is the password for admin of "/EL's Secure SecuLock Drive".) 6, Connect to "COME AT ME /EL's Secure SecuLock Drive" then log in as admin. 7, Delete DeleteMe.txt at /home. -Finding Clock.exe-You can ignore this one if you want. This would be the last thing you need to finish for Naix's "An Important Link". I didn't know how to find it, but the Lux Æterna's guide helped me alot!! If you have followed thig guide, you will need to work on CSEC's missions and find "Decypher.exe". http://steamcommunity.com/sharedfiles/filedetails/?id=498964442 CSEC Missions CSEC Invitation1, Hack "CSEC Invitation Gauntlet". 2, Read "CONTINUE.txt" at /home/Test. 3, Scan network. 4, Hack "CSEC Gauntlet 02". 5, Read "CONTINUE.txt" at /home/Test. 6, Hack "CSEC Gauntlet 03". 7, Download "WebServerWorm.exe" at /home/Gift. 8, Read "Invitation_Passwords" at /home/Test. Remember the password. 9, Reply with the password. CSEC Invitation - Affirmation1, Hack "www.cfc.com". 2, Scan network. 3, Hack "CFC Corporate Mainframe". 4, Read "11_Secret_Herbs_And_Spices.txt" at /home/training_files. 5, Scan network 6, Hack "CFC Records Repository". 7, Download "Seasoning_Order_Placement_Template_Pt1.docx" and "Seasoning_Order_Placement_Template_Pt2,docx". 8, Upload the 2 files to "CSEC Public File Drop". CSEC Invitation - Attenuation(This is what you get if you finished /el missions) 1, Hack "www.cfc.com". 2, Scan network. 3, Hack "CFC Corporate Mainframe". 4, Read "11_Secret_Herbs_And_Spices.txt" at /home/training_files. 5, Scan network 6, Hack "CFC Records Repository". 7, Download "Seasoning_Order_Placement_Template_Pt1.docx" and "Seasoning_Order_Placement_Template_Pt2,docx". 8, Upload the 2 files to "CSEC Public File Drop". CSEC Invitation - Congratulations1, Log in to "CSEC Assets Server" as admin. 2, Download "SQL_MemCorrupt.exe" at /bin/SQL_Mem_Corrupter (you don't need this if you already have "SQLBufferOverflow.exe") and "Sequencer.exe" at /bin/Sequencer. 3, Now it's time for CSEC missions.... Rod of Asclepius1, Hack "Universal Medical". 2, Search for "Jonas Sandburg". 3, Click "e-mail this record", and send the record to "gila@jmail.com". Binary Universe(ity)1, Hack "International Academic Databse". 2, Search for "John Stalvern". 3, Click "Add Degree". 4, Add the following information: "Manchester Univeristy" "Masters in Digital Security" "3.1" 5, Click "Save and Return". 6, Delete logs!! Ghosting the Vault1, Hack "CSEC Crossroads Server". 2, Download "encrypt_source.dec" at /home. 3, Hack "DEC Solutions Web Server". 4, Scan network. 5, Hack "DEC Solutions Mainframe". 6, Download "Decypher.exe" at /Staff/A.Carey. 7, Connect to your main PC, then go to /home. 8, Decrypt "encrypt_source.dec". (Use this command:Decypher encrypt_source.dec) 9, Upload "encrypt_source.cs" to CSEC Public File Drop". Imposters on Death Row1, Hack "Death Row Records Database". 2, Go to /dr_database/records. 3, Remove Joseph Felman's record. (Use this command:rm Felman_Joseph[119080]. Just type rm Felman_J, then press Tab to auto-complete the command.) Bit's disappearance Investigation1, Hack "Bitwise Relay 01". 2, Read Home_Base.txt at /home. 3, Connect to "Bitwise Drop Server", and hack it. 4, Download "READ_all_hackers.txt" at /Drop/Uploads. 5, Upload "READ_all_hackers.txt" to "CSEC Public File Drop". Through the Spyglass1, Hack "Joseph Scott's Battlestation". 2, Download "DECHead.exe" at /home/work. 3, You'll get a new email once you realy, now connect to "CSEC Crossroads Server". 4, Download "CSEC_encode_1.dec" at /home. 5, Connect to your main PC, then analyze "CSEC_encode_1.dec" with "DECHead.exe". (Use this command:DECHead CSEC_encode_1.dec) 6, You'll find an IP address for "Macrosoft Workhorse". Connect to it and hack it. 7, Read "3345633.log" at /WORKLOGS, the password is there. Red LineYou don't need to hack this server completely! Just attempting to hack it is enough! 1, Connect to "CCC Hacksquad Filedump". 2, As soon as you start hacking, you will enter "emergency recovery mode". Now you should change your IP address quickly. 3, Connect to "ISP Management System". (Use this command:connect 68.144.93.18) 4, Hack "ISP Management System". 5, Click "Search for IP", then type your current IP address. (It should be shown at bottm-left corner.) 6, Click "Assign New IP", your PC will restart immediately. 7, Reply the email. Some tips for hacking this one completely: *EASIEST WAY to beat it: Just keep hacking the server even if you enter the emergency recovery mode. Each command will reset the warning message and you will be able to finish hacking. * If you want to download the files in this server, you can do it while emergency recovery mode. You'll need to type commands really quickly though..... Wipe the record clean1, Hack "International Academic Detabase", or just log in as admin if you've done this before. 2, Search for "Jacob Stevens". 3, Click "Delete", then "Confirm". 4, Delete logs before you disconnect! Jailbreak1, Hack "Sal_Home_Workstation". 2, Scan for his eos device. 3, Log in to "Elanor Helleran's ePhone 4s" as admin. 4, Read "ids.txt" at /eos/notes, and remember the registration ID. 5, Reply with the registration ID. A Convincing Application1, Log in to "CSEC Crossroads Server" as admin. 2, Download "FOF_Screenplay.doc" at /home. 3, Analyze "T2_Screenplay.dec" with "DECHead.exe". You'll get an IP address. 4, Hack "Jason's LackBook Pro". 5, Go to /home/scripts, and upload "FOF_Screenplay.doc" from your PC. Unjust Absence1, Log in to "CSEC Assets Server" as admin. 2, Download "template.txt" at /home/Templates/DeathRowDatabaseTemplate. 3, Connect to your main PC, and open "template.txt" at /home. 4, Edit "template.txt". Use these commands: replace "[FIRST_NAME]" "John" replace "[LAST_NAME]" "Boorman" replace "[RECORD_NUM]" "111" replace "[LAST_WORDS]" "I'm ready, Warden" 5, Rename "template.txt" to "Boorman_John[111]". 6, Connect to "Death Row Records Database", and hack it or log in as admin if you have already hacked it. 7, Go to /dr_database/records, and upload the file, "Boorman_John[111]". Two Ships in the night1, Connect to "CSEC Crossroads Server", and find "C_EXE_contact.dec" at /home. 2, Decrypt "C_EXE_contract.dec" with "Decypher.exe". (Use this command:Decypher C_EXE_contact.dec quinnoq) 3, Download "C_EXE_contact.txt". (Read the txt file if you want "Clock.exe".) 4, Upload "C_EXE_contact.txt" to "CSEC Public File Drop". Project Junebug1, Hack "Universal Medical". 2, Search for "Elliot Whit". 3, Send his record to your email address. (Click "e-email this record" then "Specify Address".) 4, Go to your Jmail inbox, and read Elliot's record. You will find 2 IP addresses here. 5, Connect to "Kellis Biotech Client Services", and hack it. 6, Optional, but necessary if you wanna know what you're doing: Read all news on "Kellis Biotech News". 7, Scan network 8, Hack "Kellis Biotech Prodection Asset Server". 9, Download "KBT_PortTest.exe" at /home/Production/Output. This software will allow you to hack port 104. 10, Now go back to "kellis Biotech Client Services", and read "#0E0015_-_Pacemaker_v2.44_Firmware_and Patching" at /MsgBoard/listings. You'll find an IP address here. 11, Connect to "Eidolon Soft Production Server", and hack it. 12, Read "Eidolon_Security_Notes.txt" at /projects/Internal. Remember the user name and the password. 13, Download "PacemakerFirmware_Cycle_Test.dll" at /projects/KellisBT/Tests. 14, Connect to "KBT-PM 2.44 REG#10811", and hack it. 15, Go to /KBT_Pacemaker, and upload "PacemakerFirmware_Cycle_Test.dll" there. 16, Click "View Monitor". 17, Log in as EAdmin. (username:EAdmin password: tens86) 18, Click "Administrate Firmware". 19, Choose "PacemakerFirmware_Cycle_Test.dll", then click "Activate This Firmware". 20, Now watch his heart beat.... 21, RIP Final Missions Bit -- Foundation1, Connect to "CSEC Assets Server". 2, Decrypt "Tracekill.dec" at /bin/TK. (Use this command:decypher TraceKill.dec dx122DX) 3, Download "Tracekill.exe". Bit -- Substantiation1, Connect to "Bitwise Repo Base", and hack it. 2, Analyze "hn_repo_archieve.dec" with "DECHead.exe". You'll get an IP address. 3, Send the IP address to V. Bit -- Investigation***Use "Tracekill.exe" wisely!!*** 1, Hack "EnTech Web Server". 2, Scan network. 3, Hack "EnWorkstationCore". 4, Scan network. 5, Hack "EnTech Workstation_008". 6, Download "Prometheus.txt" at /WORKSTATION/store. You'll need the password in it later. 7, Download "StoreServIPs.txt" at /WORKSTATION/store. You'll find 2 IP addresses in it. 8, Go to "En_Prometheus", then log in as admin. (usename:adminpassword:d88vAnnX) 9, You'll get an email from V. Bit -- Propagation1, Go back to "En_Prometheus", then log in as admin. 2, Scan for eos devices. 3, Connect to "ENTECH_TEST_01's ePHONE 4S". 4, Read "nstanford@entech.com.act" at /eos/mail. Remember the username and the password. 5, Connect to "EnTech Mail Server", then log in as nstanford@entech.com. (username:nstanfordpassword:murloc33) 6, Read the email titled "Re"Romulus passwd". Remember the password. 7, Connect to En_Romulus, then log in as admin. (username:adminpassword:h7ggNKl2 <==That's small "L"! 8, Read "Contractor_Server.doc" at /STORE/Contractors. This is the admin password for "EnTech External Contractor Relay Server".. 9, Send the password to V. Bit -- Vindication1, Connect to "EnTech External Contractor Relay Server". 2, Download "heart.dec" at /Contractors/Bit. 3, Connect to your main PC, then decrypt "heart.dec". (Use this command:Decypher heart.dec divingsparrow) 4, Read "heart.txt". 5, Reply to V. Bit -- Termination1, If you don't have "Sequencer.exe" yet, connect to "CSEC Assets Server", and download it at /bin/Sequencer. 2, Run "Shell" on your main PC and some other computers. 3 or 4 recommended. 3, Start "Sequencer.exe" and click "ACTIVATE" 8, Hack "EnTech_offline_Cycling_Backup"!!! GO GO GO!!! 9, Delete all files in /ARCHIVE/Hacknet/24-02, /ARCHIVE/Hacknet/03-12, /ARCHIVE/Hacknet/18-09. 10, Delete logs. 11, Disconnect..... 12, Reply to V. Terminal1, Connect to "PortHack.Heart. 2, Hack "PortHack.Heart".......!? Final Words from Me Thank you for reading my guide. I hope my guide helped you! Anyway, if you have followed this guide too much, I recommend you to play a new session after you see the ending. Hacknet's story is pretty good and interesting, you would be pleased when you understand what was going on with those hackers, and see the ending again :D Thank you again, Gorimaccha
《黑客网络》快速完成教学任务及游戏基础学习指南 《黑客网络》是一款怎样的游戏? 《黑客网络》是一款引人入胜的终端机模拟类电脑黑客游戏。在这款带有部分剧情的游戏中,你将跟随一位近期去世的电脑黑客留下的指示,尝试找出这位黑客的真正死因。 初始接触任务 1. 查看标题为【初始接触】的邮件。 2. 返回你的个人电脑,输入【cd bin】命令进入文件系统。 3. 需要删除【bin】文件夹中的【SecurityTracer.exe】文件。删除方法为在控制台输入【rm SecurityTracer.exe】(无需引号)。 4. 再次返回邮件,点击回复新收到的邮件并发送。车辆收集任务 1. 查看名为【车辆收集】的邮件。 2. 点击链接。 3. 前往网络地图上新增的位置。 4. 在控制台输入【PortHack】以入侵电脑。 5. 在控制台输入【cd /bin】以打开bin文件夹。 6. 在控制台输入【scp SSHCrack.exe】以下载破解文件。 7. 返回邮件并回复发送新收到的邮件。 首次飞行任务 1. 查看名为【首次飞行】的邮件。 2. 点击链接并前往网络地图上的新位置。 3. 在控制台输入【probe】以查看系统端口。 4. 会出现4个端口及其代码,在控制台输入【SSHCrack 22】以访问该端口。 5. 完成操作后在控制台输入【PortHack】以入侵端口。6-完成此操作后,回复收到的邮件。 对应任务 1-查看名为【对应】的邮件。 2-点击链接。 3-前往netMap上的新位置。 4-在控制台输入【probe】检查端口。 5-端口页面打开后,在控制台输入【SSHCrack 22】以获取端口访问权限。 6-操作完成后,在控制台输入【PortHack】以控制端口。 7-获得端口访问权限后,在控制台输入【cd log】打开日志文件夹。 8-打开日志文件夹后,输入【rm *】删除日志文件夹内的内容。 9-回复收到的邮件。 此后任务 1-查看名为【此后】的邮件。 2-1.3-点击第二个链接,前往netMap上的新位置。 4-在控制台输入“probe”,等待代理服务器被找到。 5-找到代理服务器后,切换到自己的电脑。 6-如果看到【你是这台电脑的管理员】字样,在控制台输入“shell”;如果没有看到,则点击登录区域进行登录后输入“shell”。 7-输入“shell”后,返回到上一个位置,点击左侧的【过载】按钮。 8-等待一段时间后,会看到【代理已被破解】字样。 9-看到该字样后,在控制台输入“SSHCrack 22”。 10-然后使用“PortHack”命令。11-获取端口访问权限后,输入“cd home”进入home文件夹。 12-打开home文件夹后,输入“scp Entropy_Induction_Test”下载Entropy_Induction_Test文件。 13-回复收到的邮件并发送。 验证任务 1-查看名为“Onaylama”的邮件。 2-点击链接并前往netMap上的新位置。 3-在控制台输入“probe”。 4-看到“Proxy Bulundu”字样后,点击【过载】按钮。 5-等待一段时间后,在控制台输入“SSHCrack 22”并打开端口。 6-使用“PortHack”命令获取端口访问权限。 7-输入“cd MsgBoard”打开MsgBoard文件夹。 8-执行“rm config.sys”命令删除“config.sys”文件。 9-回复收到的邮件并发送。任务的结束 完成这些任务后,你将带着新的指令和新的团队继续调查Bit的死亡。你仍然会收到任务,但现在你可以在没有教程指导的情况下独立完成这些任务了 :)
使用Hacker的方式探索HackNet 前言 1. 本攻略适合已经完成一周目,并尝试探索hacknet中没有尝试过内容的同学,如果是新手,建议参考其它攻略 2. 本攻略近可能的覆盖了游戏中的所有元素,但难免挂一漏万,如有错漏,请各位同学评论区指正 3. 游戏中所有使用静态地址和提供密码的,本攻略都标记了出来,如果没有写,则表明这些电脑使用的是随机生成的地址和密码。切记静态密码只有在初始状态下才有效,如果对电脑进行了破解,原始密码会被程序自动更换。 3. 对于攻略中提到的需要编辑脚本实现的“features”,请研究一下游戏安装目录下content目录的内容,作者没有修改的脚本。 4. github上有一个openhacknet的项目,如果你懂C#并愿意折腾,可以做出一个新的hacknet。 5. 本体任务中提到的“扫内存”操作,是DLC引入的新功能,扫描内存获得电脑过去的操作记录。使用的工具,会在DLC任务里出现,并有专门的任务说明该工具的使用方法。如果还没有完成DLC任务,请暂时忽略该功能。如果没有购买DLC,请永久忽略。 入门任务 1.初次联系 目标:删除SecurityTracer.exe, 电脑:本机 2.让我们来一起获取一些工具 目标:下载到工具SSHCrack 电脑:毒蛇 - 作战基地 PS:可扫描到eos设备“Tim 的 ePhone 4S” PS:可扫到电脑Entropy 资源缓存,里面有HexClock程序 PS:可以直接完成“生涯起点”任务,任务2,3,4将被跳过。记得先从1337.1337.1337.1337下载所有工具。 3.初试牛刀 目标:获取“Bitwise 测试PC”电脑控制权(密码:随机) 电脑:Bitwise 测试PC 4.善始善终 目标:删除log目录下内容 电脑:P. Anderson的卧室电脑 5.生涯起点 目标:下载文件Entropy_Induction_Test 电脑: Entropy 测试服务器 (ip=199.59.149.230) Entropy任务 说明:Entropy任务采用计分制决定游戏进度,每完成一个任务得到1分(不包括任务1,2,3)。隐藏任务触发条件如下: 3分 触发eosDevice任务,即任务8,9 4分 触发DLC任务 5分 触发Naix分支任务,即任务11,12,13 1.任务完成 目标:删除MsgBoard目录下的config.sys 文件 电脑:Slash-Bot 新闻网 2.欢迎 目标:获取“Entropy 资源服务器”电脑控制权(密码:rosebud) 电脑: Entropy 资源服务器 3.Re: 欢迎 目标:访问“Entropy 任务数据库” (密码:rosebud) 电脑:Entropy 任务数据库 以下为Entropy 任务数据库任务 4.Point Clicker 目标:删除PointClicker/Saves目录下的Mengsk.pcsav 文件 电脑:PointClicker (密码:pointsIsLove) 5.经典的反黑客攻击 目标:删除home/WORKSPACE目录下的SECURE_MAILLIST.dec 文件 电脑:PP市场公司(密码:willsmith) PS: SECURE_MAILLIST.dec文件解密后的内容: IP=74.125.237.119(JMAIL) HEADER= Marketing encryption lv.2 内容: 我耍你玩呢, 你个菜鸟黑客, 我怎么可能把重要的数据文件就这么放在公开服务器上? 尤其是当我们知道有人正在觊觎它的时候. 来, 送给你点垃圾二进制数据, 这样文件的大小看起来才合适. (一堆乱码二进制) 爱你的, 一位真正的信息安全专家 XOXO 6.重回学校 目标:回复密码(七个*) 电脑:Milburg高中IT办公室(密码:*******) 7.X-C 项目(Entropy StartingSet Entropy04.xml) 目标:回复正确的项目代号(1299) 电脑:X-C Project Tablet#001//RESEARCH(密码:cyberdisk) PS: 回答文件里的任何一个ID号都可以正常结束并得到加分,但会得到正面或负面回应两种结果。具体如下: 回复(1299,1938,2133, 1300)收到邮件: 干得不错, 我相信你并不是靠运气蒙对ID的. 这确实是我想要找的那类文件. 希望我们团队在这个项目上所付出的汗水在将来能得到回报. 谢谢, 回复(4991)收到邮件: 呃, 好吧. 你这活干的... 有点不太专业啊. 我想... ..我还是和我们的博士讨论一下今后如何合理使用项目资源吧. 谢谢你, 这件事我还是自己来搞吧. 8.eOS设备扫描 目标:回复手机持有者的邮箱账号的密码(tintin7) 电脑:Jason's PowerBook Plus -> eos设备Jason's ePhone 4S 9.粉碎N的攫取 目标:回复手机记录的密码(warsix22) 电脑:JDel家庭电脑->eos设备 Jacob's ePhone 4 10.删除文件任务1,2 (随机) 目标:删除邮件指定服务器上的指定文件 电脑:随机 PS:服务器任务列表里的删除文件任务共2个,由程序根据模板随机生成。程序不阻止使用相同的模板,即得到的任务可能内容完全一样,仅仅公司名和文件名不同。模板共有6个,具体如下: 阻止非法收集 清理程序 恐吓手段 疏漏的数据 偿还政策 我们的产品是独一无二的 PPS:游戏目录其实还包含了一个”改变网站内容“的任务模板,但在程序中没有激活。这些任务需要改变目标网站html文件的一些内容,且目标电脑需要解开4个端口。这些任务完成后,每个任务会得到5分的加分。如果想激活这些任务,有两个方法: b1. 将” 改变网站内容”模板里的内容拷贝到”任务删除“模板文件中 b2. 修改程序(提示,请见前言第5点) 修改只需要几行(< 10)代码就可以完成了 ”改变网站内容“的任务模板有3个,分别是 破坏招聘 揭开事实真相 招聘活动 11.入侵行为必须受到惩罚 目标:删除home目录下的Macrosoft_Internal_Raid_Archive.rar 文件 电脑:代理_节点-X04(ip= 173.194.35.163) PS:该任务完成后,会触发“Naix的复仇”事件,本机被攻击。机器恢复后,根据不同的动作,可触发多个分支,具体如下: A1: 什么都不做,直接回复该邮件,跳转到12 A2: 回复邮件” Are you Kidding me? “ 内容包含”FXXK“,得到Naix的邮件(Fxxk you too),该动作不影响后续发展 A3:查找攻击源,从”代理_节点-X22”查找到” Naix 基地网关“(ip= 173.194.35.172,密码= roxxane)删除home目录下的Macrosoft_Internal_Raid_Archive.rar",跳转到13 A4:查找攻击源,从”代理_节点-X22”查找到” Naix 基地网关“(ip= 173.194.35.172,密码= roxxane)删除sys目录下的x-server.sy",跳转到Lelzsec任务 PS:完成DLC任务后,在Naix 基地网关扫内存,可以得到Pellium Box电脑(ip= 69.172.201.153) 12.希望这么做能派上点用场 目标:找到备份文件的服务器地址(168.61.82.246),并在邮件中回复 电脑:KyonBox (ip= 176.194.38.111,密码= haruhi) PS:备份文件服务器名称”巨硬仓库服务器“,服务器上有主题文件GOLD-Theme.sys 13.恭喜 目标:无,稍后会转到MainHub任务 电脑:无 Lelzsec任务 1.gg wp 目标:把index.html里面的”nortron“替换成”XXXXX“(违禁词) 电脑:Nortron 安全网络服务器 PS:电脑防火墙密码NORTRON 2.节目效果爆炸 目标:获得电脑” Nortron 中央服务器“的控制权 电脑:Nortron 安全网络服务器-> Nortron内部服务器->获得J.Abrams的邮箱密码bootyking420-> Nortron邮箱服务器->获得Nortron 中央服务器的防火墙密码123456789ABC-> Nortron 中央服务器 PS:Nortron邮箱服务器防火墙密码也是123456789ABC 3.一个重要的链接 目标:无,稍后会转到Lelzsec论坛 电脑:无 4.北极星试炼 目标:获得”北极星之首“的服务器控制权,获得文件WHITE_x-server.sys SQLBufferOverflow.exe(SQL破解工具,稍后也可获得,文件名不一样,功能完全一致) 电脑:北极星之圣所(ip=103.31.7.34),网页源码有四个站点ip 北极星 - 耐心之试炼(ip=103.31.7.38) 得到IP第一段103 北极星 - 急速之试炼(ip=103.31.7.41) 得到IP第二段33 北极星 - 勤奋之试炼 (ip=103.31.8.1)-> 勤奋之尾(ip=103.31.8.2)得到IP第三段8 北极星 - 专注之试炼(ip=103.31.7.211)得到IP第四段 162 北极星之首(ip= 103.33.8.162) PS:北极星 - 专注之试炼防火墙密码MALICE,北极星 - 勤奋之试炼防火墙密码SNAKE,勤奋之尾防火墙密码FANG PS:完成DLC任务后,扫内存可以得到The Gibson电脑,得到ClockV2.exe。 PS:内存的内容除了英文版都有问题,如何修复请看我的另一篇指南。 5.破解SecuLock 目标:删除home目录下的DeleteMe.txt 电脑:来黑我呀 /EL SecuLock 安全驱动(ip=69.172.201.208,密码= ithoughtyouweremakingtea) PS:论坛相关网页里还有另外一个地址Stormrider(ip= 199.89.130.68,密码= ithoughtyouweremakingtea ),破解后可以找到程序WebServerWorm.exe,以及eos设备” Mica's ePhone 4S “,在eos设备的note目录里就有目标电脑的密码(ithoughtyouweremakingtea) 6.一次胜利, 一次可能成为转折点的胜利 目标:无,在完成任务4,5后触发,稍后转到CSEC任务 电脑:无 CSEC任务 说明:如果是从Lelzsec任务进入的,则不会出现任务1,该任务同样采用计分制,完成一个任务1分,但其实总分数并不起作用,因为只有清空任务列表里的所有任务,才会跳转到下一个任务集(Bit任务)。其它隐藏任务触发条件如下: 1分 触发ThemeChanger事件,hub资源服务器里会添加ThemeChanger程序 2分 触发DLC任务,如果没有在Entropy任务里触发DLC,在这里会再次给出DLC任务的入口(这是最后一次进入DLC的机会了) 4分 触发Bit失踪调查,即任务14 7分 且完成了任务 8, 10 触发”甲虫计划”, 即任务16 10分 且任务列表清空(所以这个10分的触发条件实在设的没什么意义),触发下一个任务集(Bit任务) 1.来自CSEC的邀请 目标:获得测试服务器密码(ABX07cc9),并在邮件中回复 电脑:CSEC 邀请中继(pass= easy)-> CSEC 中继 02(pass= medium)-> CSEC 中继 03(pass= victory) PS: 密码在home/Test下的Invitation_Passswords中,同时服务器上有WebServerWorm程序 PS:CSEC 中继 03防火墙密码KUNKKA,CSEC 邀请中继防火墙密码KRAKEN 2.来自CSEC的邀请 - 批准/难以置信 目标:上传啃得鸡模板文件Seasoning_Order_Placement_Template_Pt1、2.docx 电脑:www。cfc。com->啃得鸡XX主页->啃得鸡记录库(ip= 202.7.177.65) PS:啃得鸡记录库防火墙密码CHICKEN 3.消除记录 目标:删除Jacob Stevens的学位记录 电脑:国际学术数据库(ip=129.67.0.11) PS:防火墙密码ACADEMIC 4.二进制宇宙(大学) 目标:按照邮件提示修改学术数据库数据 电脑:国际学术数据库(ip=129.67.0.11) 5.死亡名单上的冒充者 目标:删除死亡数据库数据Joseph Felman 电脑:死亡人员名单数据库(ip= 168.51.178.4,pass= texas) PS:防火墙密码AHSUNYAG 6.缺失的正义 目标:上传boorman的文件到死亡数据库 电脑:死亡人员名单数据库(ip= 168.51.178.4,pass= texas) 7.一份有说服力的申请 目标:上传FOF_Screenplay.doc的文件到电脑”Jason's LackBook Pro“ 电脑:Jason's LackBook Pro (ip=37.187.27.55,pass=DANGER) PS: 电脑上的加密文件 T2_Screenplay.dec, 无密码,剧本是”泰坦尼克2: 冰山的复仇” GHL_ChapterList.dec, 无密码,剧本是” 银河英雄传说” PS:电脑防火墙密码也是DANGER 8.潜入宝库 目标:解码文件encrypt_source.dec 电脑:DEC方案小组网络服务器-> DEC方案小组主页(ip= 101.0.89.154)->查找 Staff/A.Carey目录里的Decypher.exe PS: 1. Staff/J.Scott/Decypher_Test.dec, Staff/J.Scott/Encryption_Base2.dec, home/encrypt.dec 三个加密文件没有密码,里面的cs源码文件,是真实的Hacknet程序加解密功能的函数,而且加解密方法很有趣(划重点: 不难) 2 . Staff/D.Leatrou/Personal_Notes.dec和Staff/D.Leatrou/Lawsuit_Response.dec的内容极易引起三观炸裂,请谨慎观看。密码:dleatrou (密码在DEC方案小组网络服务器的文件上可以找到线索) PS:DEC方案小组网络服务器防火墙密码ENCRYPT 9.夜晚的两艘船 目标:解码并上传文件C_EXE_contact.dec 电脑:无 PS:文件里提到一个JMail账号名为dlocke,账号密码sandalphon。邮箱里的” Tick Tock “提到地址24.43.69.78,指向服务器”Timekeeper的宝藏” 服务器上的Clock.dec密码为yuna,(发信人账号叫yunafans)可以得到Clock程序 10.透过'潜望镜' 目标:下载文件Dechead.exe 电脑:Joseph Scott的作战基地 PS:home/work/Decypher.dec 没有密码,解开后是程序Decypher.exe 11.回复 : 透过"潜望镜" 目标:获得文件CSEC_encode_1.dec的密码并在邮件回复(beepbeep) 电脑:巨硬 重负荷服务器 04(ip=168.61.82.245) PS:目标地址通过Dechead解析CSEC_encode_1.dec获得,密码在WORKLOGS/3345633.log里 12.警告线 目标:无目标 电脑:CCC 黑客小队 文件转储 PS:可以直接回复邮件通过,目标服务器”CCC 黑客小队 文件转储”追踪程序时间仅仅2.5秒,要想破解可通过如下手段 a.直接使用密码honeypot(仅第一次破解有用) b.修改Content Missions MainHub Misc HoneyPot01.xml,找到<trace time="2.5" />,把2.5改成一个比较大的数值,比如60. (需新建账号生效) c.直接修改存档文件,思路同上 破解完成,会得到Honey_x-server.sys 13.医神之杖 目标:找到Sandburg记录并发送到gila@jmail.com 电脑:通用医疗( ip=208.93.170.15, pass= codeine) PS:防火墙密码MEDICATE 14.Bit失踪调查 目标:找到READ_all_hackers.txt并上传 电脑:Bitwise 中继 01(pass= test)-> Bitwise共享服务器(ip= 108.160.165.139,pass= test)-> Drop/Uploads目录 PS:Bitwise共享服务器防火墙密码breezer 15. (手机)越狱 目标:找到注册ID并在邮件回复(AAX1BB7) 电脑:Sal_家_工作站->Elanor Helleran's ePhone 4S->note目录 16.甲虫计划 (7分且完成8,10) 目标:杀死Whit或者回复Deny(游戏允许该任务不执行) 电脑: KBT-PM 2.44 REG#10811(ip= 202.6.141.219)网上这一关攻略很多,就不详细写了 PS:如果不想做这个任务,回复邮件并附加信息”deny“,系统会回复邮件说”麻烦你了“。如果你的分数够到下一个任务集,直接回复该邮件,就会收到Bit任务的邮件。 PS:Kellis生物科技客户服务器和Kellis生物科技产品资源服务器防火墙密码都是BIOGEL PS:除了PacemakerFirmware_Cycle_Test.dll之外,其他dll文件下载替换都可以正常工作,不会有任何副作用。 Bit任务 1.Bit -- 初章 目标:无 电脑:无 PS:可以先下载并解密TraceKill.dec,不解也不会影响后续流程 2.Bit -- 证明 目标:获得并在邮件回复可疑服务器地址(156.151.59.35) 电脑:Bitwise Repo 基地(ip=23.236.62.147, pass=tenzen)-> 解析hn_repo_archive.dec文件头 –>EnTech 外部承包商中继服务器(ip=156.151.59.35, pass= ax889msjA) PS: hn_repo_archive.dec的密码ax229msjA,但是解密后只能得到一堆二进制数 “EnTech 外部承包商中继服务器”和后面的任务相关,这个任务最好不要访问,以免造成后面任务流程混乱。 PS:该电脑可以扫内存 3.Bit -- 调查 目标:获得电脑En_Prometheus控制权 电脑:EnTech 网络服务器(pass=ax889msjA)->En工作站核心->EnTech工作站 _008(ip=156.151.0.42)->WORKSTATION/store/Prometheus.txt->En_Prometheus(ip=156.151.1.1, pass=d88vAnnX) PS: 相关电脑: EnTech工作站 _001/003/004/012 都是空电脑,就不用好奇进去看看了。 EnTech_宙斯 密码:v19328hQ9。作者曾设定最后一个任务的目标是删除这个服务器上的文件,后来变成了离线服务器(使用sequence),大概觉得这个服务器不够酷吧 4.Bit -- 蔓延 目标:获得EnTech 外部承包商中继服务器密码(ax889msjA) 电脑:En_Prometheus->eos设备 ENTECH_TEST_01's ePhone 4S->邮箱账号nstanford(pass= murloc33)-> En_Romulus密码(pass = h7ggNKl2)-> STORE/Contractors/ontractor_Server.doc PS:ENTECH_TEST_02's ePhone 4S这台设备里提示不要放敏感数据,而且真的没有敏感数据 5.Bit -- 澄清 目标:无 电脑:无 PS:本来这个任务的目标是下载上个任务服务器中的heart.dec文件,不过被作者删除了。想想也确实意义不大。 6.Bit -- 阻止 目标:删除EnTech_离线_循环_备份的ARCHIVE/Hacknet下的所有文件 电脑:EnTech_离线_循环_备份(使用sequence激活) PS: 防火墙密码EMMETPLACE 7.Bit -- 终章 目标:无 电脑:无 8.尾声 目标: 破坏Porthack.心脏 电脑:Porthack.心脏 9.额外的馈赠 任务通关后出现服务器 制作组及花絮(ip=226.187.99.3),并且在下周目开启时出现服务器(1337.1337.1337.1337),里面有全套的基本工具。 DLC任务(Labyrinths) DLC任务共有两个入口:Entropy和CESC任务服务器的合同列表。两个入口对DLC任务流程没有影响,只有一些细节不一样,后面会提到。 1.Kaguya的试炼 目标:运行目标电脑的KaguyaTrials程序 电脑:Kaguya来源 PS:该电脑可以得到FTPSprint程序,这个程序破解速度比FTPBounce快的多 PS:kenobi.dec的密码Obi-Wan,解密后会得到一份很“感人”的邮件 PS:x-server.sys其实是一个隐藏的主题miami light,建议改名后下载 2.kaguya1(试炼内容1) 目标:清空sys文件夹 电脑:Kaguya冲刺试验(ip=74.125.23.121) PS:可以下载到TorrentStreamInjector.exe PS: 可以下载到Miami_x-server.sys主题 3.kaguya2(试炼内容2) 目标:删除Kaguya推送试炼的文件Delete_Me.txt 电脑:Kaguya推送试炼(ip= 216.239.32.181) 4.定制狂 目标:上传加密文件SSLTrojan.dec 电脑:Ricer个人电脑 PS:WIP_SSLTrojan.dec和SSLTrojan.dec都没有密码,且内容都一样,是SSLTrojan程序。 PS:电脑有Themechanger可下载 PS:可以扫出memdump,但是没有有效信息 5.DDOS攻击出现在一些重要的服务器上 目标:清空L. Shaffer的笔记本和r00t_Tek战斗基地的LOGIC目录 电脑:L. Shaffer的笔记本,r00t_Tek战斗基地 6.炼金术师 目标:上传SignalScrambler程序 电脑:School of the Hermetic Alchemists-> HA_Rebis(ip= 66.96.149.16)-> Nate's ePhone 4S(eos设备)-> Nate Wesson的家(ip= 66.175.58.9) PS: 电脑HA_Coagula没有任何有效信息 PS:电脑HA_Solve上的文件info.dec没有密码,记录了HA_Rebis的防火墙密码clarity,同样的信息在IRC频道也有。 PS:电脑Nate Wesson的家扫内存,可以发现电脑STOR-DRIVE(ip=66.175.58.11),还有一张炼金术士的图片。 PS:电脑STOR-DRIVE可以发现DNotes.exe 7.内存取证(1/3) (与任务8二选一) 目标:删除文件SN_MF_Decompiled.zip 电脑:dump_1.md->iodependency~Atlas(ip=88.29.144.6) PS: dump_1.md里面的另外一个IP(167.72.73.56)指向Snackintosh_中继,但没有什么有效信息 PS:iodependency~Atlas和Snackintosh_中继的管理员密码都是4TL4S PS:dump_2.md可以找到Snackintosh_代理(ip=185.160.171.69),同样没有什么有效信息,且管理员密码也是4TL4S 8.内存取证(2/3) (与任务7二选一) 目标:删除文件sn_memory_dump_decompiled.rar 电脑:dump_4.md-> Lihota产品(ip=17.5.3.9) PS: dump_3.md里面无有效信息(IP是个无效地址),可以不分析 PS:Lihota产品的管理员密码也是4TL4S 9.内存取证(3/3) (非任务) PS: dump_5.md里面包含了Raven Dataworks(ip= 208.73.49.146)的地址,可以下载程序ComShell.exe PS:dump_6.md里面包含了一个马尔可夫链的笑话(恶寒…) 10.Striker藏匿处 目标:上传程序MemDumpGenerator.exe 电脑:Striker缓存(ip=72.52.4.117) PS: 任务完成后会被StrikerR攻击,恢复电脑后(这个恢复过程绝对脑洞大开,且linux系统下的恢复过程更合理一点),可以跟踪到Striker代理(ip=72.52.4.119)和Striker_攻击位置(ip=72.60.4.119),在Striker_攻击位置可以找到一批主题文件。 PS:如果是在CSEC任务进入的DLC,在Striker_攻击位置删除uni目录下的内容,会得到StrikerR的“问候邮件” 11.It Follows(与任务12二选一) 目标:清空TortillaVPS的home目录 电脑:cornch1p家庭电脑(ip=177.3.200.6)->扫内存->MagmaMailbox( ip=26.26.62.62 username=cornch1p password=SaltyChippies22)-> TortillaVPS(ip=7.201.4.178) PS: MagmaMailbox有主题文件caution_standard_x-server.sys 12.清除(与任务11二选一) 目标:清空佛兰克斯坦的实验室的home目录 电脑:佛兰克斯坦的实验室(ip=21.32.43.54) PS:扫内存可以发现佛兰克斯坦的地下室(ip=32.43.54.65),可以找到一堆dec文件,但没有有效内容 13.Neopals 目标:把用户minx的Neopoints修改到大于999999。 电脑:Neopals主页->Neopals_版本控制(pass=undc321b9y)-> Tiff Doehan_个人PowerBook(ip=98.129.229.204,pass=ixidixie)-> Tiff的ePhone 7(eos设备)-> Neopals_身份验证(pass=mlk3fsdie321)->扫内存->Neopals_主机(pass=n8u5v432kj) PS: Thomas_办公室没有有效内容 PS:Ash-ALIENGEAR13扫内存可以得到一张坦克图片 14.豆茎(与任务15,16三选一) 目标:上传文件038457_doc.pdf 电脑:梅丽山咖啡馆路由器(ip=198.216.105.54)->Asdis Dagrunsdottir的笔记本电脑(ip=198.150.137.83)->扫内存->Manananggal_工作簿(ip=244.188.232.231) 15.Expo Grave (与任务14,16三选一) 目标:上传4个文件:上传p_SQL_399.gz到Howard Grave的个人电脑、SecurityCoNnEXION网页门户、Howard Grave的ePwned+-, 上传patch_checksum.chk到Howard Grave的ePwned+-。 电脑:Howard Grave的个人电脑-> Howard Grave的ePwned+-(eos设备),SecurityCoNnEXION网页门户 PS:Howard Grave的ePwned+-是唯一一台admin密码不同的eos设备,密码fma93dK 16.键盘人生(与任务14,15三选一) 目标:删除home/records目录下的purchase_blacklist.txt 电脑:ClickLab产品 PS:电脑文件layout_wip.txt包含了一个键盘编辑器网页 http://www.keyboard-layout-editor.com/#/gists/0ffdf87af5ba50af1a1018052012832b, 扫内存可以找到一个键盘收藏照片网址 http://imgur.com/a/B1Iox 17.夺机 目标:获得太平洋航空_预售服务器的管理员密码 电脑:LAX_太平洋_服务器->太平洋航空网络中心->太平洋航空_白名单_验证器->Faith Morello的笔记本电脑(ip=209.68.11.125)->Vito McMichael的笔记本(ip=209.68.41.129)->Faith Morel的笔记本电脑(获得IRC账号密码username= faithless, pass= catsarebestpet)Psylance网络安全雇员IRC(ip=50.31.225.93)-> Kim Burnaby的办公室电脑(ip=141.8.224.143)-> 太平洋航空_邮件(username=kburnaby pass=noneofyourbusiness)-> Yasu Arai的触屏电子书(ip=141.88.107.140, pass=1185JACK1)-> Yasu's ePad Plus(eos设备)-> 太平洋航空_预售服务器(重置密码)-> 太平洋航空_邮件(username=YasuArai, password=9NINETWO2) PS: Kim Burnaby的办公室电脑可以扫到eos设备Kim's ePad XL,但没有有效内容 PS: 太平洋航空_邮件的所有账号密码 username=awilburn pass=1234 username=kburnaby pass=noneofyourbusiness username=YasuArai password=9NINETWO PS:Mark Robertson的办公室电脑(ip= 98.124.245.24)没有有效信息,可以不访问。 PS:记得在Faith Morello的笔记本电脑下载PacificPortcrusher.exe 18.搭乘_航班内容 目标:上传sysinfo.bat到太平洋_ATC_Skylink的sys目录 电脑:太平洋_ATC_路由中心->扫内存->太平洋_ATC_白名单验证器(pass= CKYX258)-> 太平洋_ATC_Skylink" (ip=208.91.196.94) 19.坠机 目标:上传747_FlightOps.dll到PA_747_0022机载电脑 电脑:PA_747_0018机载电脑(ip= 208.73.211.70)-> PA_747_0022机载电脑(ip= 209.15.13.134) PS: 这个任务也可以什么都不做,让PA_747_0022坠毁,甚至可以删除PA_747_0018上的dll,让两架飞机都坠毁。如果这样做,将会跳到任务21. 20.毁灭痕迹 目标:清空Kaguya_网关上的bin和sys文件夹 电脑:Kaguya_网关(ip=54.183.231.31) PS:trnt.exe就是torrent程序 PS:trialSources.txt里是真实的kaguyatrail.exe的内容 21.最后一幕 目标:无 电脑:Kaguya_计划(ip=54.183.231.34) PS:本电脑可得到程序Tuneswap.exe和NetmapOrganizer.exe PS:请扫一下本电脑的内存 PS:根据内存的内容,可以找到Labyrinths_DevChat(ip=54.192.133.33),里面是开发者的聊天记录 22.额外任务:让Psylance沉默(在CSEC任务出现) 目标:删除2_q1.zip,并且上传PA_0022_Incident.dec到Psylance内部服务 电脑:Psylance内部档案(pass=faithless),Psylance内部服务(pass=catsarebestpet) PS:请在替换PA_0022_Incident.dec前保存原来的文件 PS:该文件没有密码,解开后可以发现Coel__Gateway的地址(ip= 208.73.210.214) PS:Psylance内部服务可以扫内存 补遗:DLC任务中有一台神秘的服务器“Bibliotheque影子存储器”,IP地址是随机的,安全级别也是最高的。里面存储了DLC任务中所有用到的文件,通过存档文件和脚本修改可以把这台服务器暴露出来。 最后的补遗:DLC任务中应该有一台电脑Kaguya中心(ip=216.239.32.21),不过我实在没有发现游戏里有线索可以进入。如果谁知道的,可以留言给我。(已确认,不会出现,必须要修改脚本) 附录 1.Jmail邮件服务器所有账号密码 username="dlocke" password="sandalphon" username="gila" password="420PraiseIt" username="vapor" password="d771njk38A" username="exxuaanne" password="182736189" username="naix" password="roxxane" username="jjstacks" password="tintin7" username="sal" password="22foxhound" username="micasa" password="ithoughtyouweremakingtea" 2.Entech邮件服务器所有账号密码 username="nstanford" password="murloc33" username="hnManager" password="hnmanager22" username="bcarter" password="dota4lyf" username="rc" password="byC89kMMe" 3.永远不会出现的服务器 www.reddit.com 游戏作者在任务里定义了该服务器,但没有引入。 4. 关于任务检查的bug 游戏中关于文件修改的任务,如果第一次修改的内容不正确,后面改正再确认,还是不会被通过的。 解决也很简单,保存退出到主界面,再进入,就可以正常判断了。 5.工具大全 a. 跟随任务进度即可获得,无需寻找: Tutorial.exe SSHcrack.exe FTPBounce.exe SMTPoverflow.exe WebServerWorm.exe Notes.exe SecurityTracer.exe SQL_MemCorrupt.exe Decypher.exe DECHead.exe KBT_PortTest.exe TraceKill.exe eosDeviceScan.exe Sequencer.exe b. 在本体游戏出现,需寻找: Clock.exe HexClock.exe c. 在DLC任务出现,无需寻找: KaguyaTrial.exe themechanger.exe TorrentStreamInjector.exe SSLTrojan.exe FTPSprint.exe SignalScramble.exe MemForensics.exe MemDumpGenerator.exe PacificPortcrusher.exe NetmapOrganizer.exe d. 在DLC任务出现,需寻找 ComShell.exe DNotes.exe ClockV2.exe Tuneswap.exe e. 扩展模式出现,但可通过编辑脚本加进游戏: RTSPCrack.exe ESequencer.exe OpShell.exe(强烈推荐) f. 一个玩笑 hacknet.exe(只会在终端输出程序已运行的文字) 6.关于游戏版本 Hacknet定义了demo,alpha,pressbuild等多个版本,每个版本引用的任务都不太一样。甚至在某个版本,通关后matt大大会给你一封邮件,告诉你不要玩盗版!
奈克斯不会料到这一招…… 如何备份 奈克斯会删除你的x-server.sys。 你必须通过不同的用户界面恢复x-server。 我不喜欢这样。 重启存档后,我是这么做的: 1.完成教程或获得【Quickdraw】成就。 2.进入/sys文件夹。 3.运行命令:scp x-server.sys ../home 4.此时你的电脑/home目录下会有x-server的副本。 如何恢复 1.当你遇到问题后,输入cd /home 2.运行scp x-server.sys ../sys 3.使用reboot -i命令重启 4.现在你可以继续游戏了。
A completely spoiler-filled guide on how to do every mission in the DLC. General Tips Type your commands out ahead of time so you can run them as fast as possible Use FTPSprint instead of FTPBounce. It's way faster Use the "ps" and "kill [id]" commands to stop TorrentStreamInjector whenever it's done. You'll save time If stuck, investigate every route. I mean EVERY route. You should be scanning everything you hack into. eosDeviceScanner should be used on all personal computers. MemDumpGenerator should be used when you've tried everything else There will be things you literally can't get past, and that's okay. Unlike in the main game, you're working in a team. If you find something you can't move past, try investigating everything else first. Your teammates might come up with a solution for you If you're stuck, also consider going back over the mission requirements. Labyrinths has a heavier focus on investigation, imo. If you can't figure something out, there's a good chance you missed or forgot something Kaguya Source Connect to the IP given in the email. (Need the email for this? There's a guide here.) Hack into the server Hop on into /bin and pick up FTPSprint.exe and KaguyaTrials.exe Whenever you're ready, run KaguyaTrials and click "BEGIN TRIAL" Kaguya Sprint Trial (Second Test) Connect to the given IP and hack in Get TorrentStreamInjector.exe from /bin Delete all files in /sys Disconnect Kaguya Push Trial (Third Test) Connect to the given IP and hack in Delete the file in /home Disconnect The Ricer Connect to the given IP and hack in Move to /home/projects and grab SSLTrojan.dec WIP_SSLTrojan.dec Grab ThemeChanger.exe if you want Go to the drop server and upload SSLTrojan.dec After completion, get SSLTrojan.exe from the drop serverNOTE: If you have Decypher, you can decrypt the file to get SSLTrojan.exe, but uploading it won't count for accomplishing the mission. You have to upload the encrypted file. If you don't have Decypher, upload the encrypted file and they'll decode it for you. You just have to hack into the upload server log in to the upload server like a normal person to get it. The password is given in the chat. DDOSer on some critical servers Connect to the given IP and hack in DESTROY EVERYTHING Scan the network Hack into the connected computer DESTROY EVERYTHING The Hermetic Alchemists Connect to the given IP and hack in Scan the network Hack into Coagula and Solve Try to hack into Rebis, and you'll notice it's not that easy. D3f4ult helps you out though. In the chat, you get the solution for the firewall: "clarity". Hack into Rebis Use eosDeviceScan and get admin access Poke around and see if you can find where he might have it. Go to /eos/notes/home.txt and connect to the "Home" IP address you find Hack into the computer you find Get SignalScramble.exe from /bin Upload it to the drop server Memory Forensics (1/3) Go to the drop server and pick up MemForensics.exe from /bin Staying on the drop server, navigate to /home/MemoryDumps Run MemForensics on the first of your md files (Kaguya_Dump_1.md in this case) Process recent commands. You'll find two working IP address and a useless username and password Connect and hack into the first IP. There's a decompiled MemForensics in /home! For shame! DESTROY EVERYTHING Connect and hack into the second IP you find. Poke around a bit There isn't any sign of MemForensics here. Leave Run MemForensics on the second of your md files (Kaguya_Dump_2.md in this case) Process files in memory. You find a lot of defunct IP addresses... and one working one. Connect to it and hack in No sign of anything here, either. You're done Memory Forensics (2/3) Go to the drop server and pick up MemForensics.exe from /bin Staying on the drop server, navigate to /home/MemoryDumps Run MemForensics on the first of your md files (Kaguya_Dump_3.md in this case) Process files in memory. You'll find an IP address that doesn't exist along with a username and password that don't work. Nothing to do here Run MemForensics on the second of your md files (Kaguya_Dump_4.md in this case) Process recent commands. You'll find a working IP address. Connect and hack in Navigate into /share/secure. There are copies of MemDump files! Naughty! DESTROY EVERYTHING Striker's Archives Connect to the given IP and hack in Pick up MemDumpGenerator.exe from /bin Upload it to the drop server HACKED! This does not happen to everyone. It depends on whether or not Striker can find your IP address, which depends on how you disconnect from the computer (hint hint). If you get that message about an incoming connection, though, you have two options: DON'T GET HACKED: Very quickly go to your PC and set up a shell Hit "trap" on that shell and confirm itYou'll be given a slight reboot and can continue where you were. GET HACKED: Wait patiently and watch your computer freak out Coel will appear to help and give you some instructions. Hit "proceed" when you're ready Use either the terminal or your computer's file explorer (whichever one you find easiest) to track down the file "VMBootloaderTrap.dll" and delete it. Information on how to do so is below. Close the text file and terminal and restart Hacknet (the game itself) Optional: At your teammates' suggestion, get revengeEverything should start up again and you can continue. Using the TerminalThe terminal should start you off in /Hacknet. Use the change directory command to navigate to /Libs/Injected There should be a file named "VMBootloaderTrap.dll" in that folder. Use the delete/remove command to delete it If you need to check what's in the folder you're in, use the directory/list command Commands Windows: "cd [directory name]" - Change directory. Works the same as in Hacknet. Moves you from one folder to another. Putting ".." as the directory name will move you up one folder. "dir" - Directory. Lists all files and folders in the current directory. "del [file name]" - Delete. Deletes the file. You don't need additional permissions to delete it.Mac/Linux: (All work the same as in Hacknet) cd - Change directory. Moves you from one folder to another. Putting ".." as the directory name will move you up one folder. "ls" - List. Lists all files and folders in the current directory. "rm [file name]" - Remove. Deletes the file. "icacls VMBootloaderTrap.dll /grant USERS:d" - This is used once you find the file to give it the permissions you need to delete it. Type it in exactly. Using your File Explorer(Thanks to PhoenixBlue44 for describing how to do this on Mac) Open up your file explorer and navigate to the file location You might not be able to see the folder you need to find. If so, follow the instructions below: Windows:Open up your control panel Go to "Appearance and Personalization", then "Folder Options" Hit "Show hidden files and folders" You should now be able to find the folder you needMac: In your user folder, right click to bring up the view options Select "Show View Options" then "Show Library Folder" Move on to "Application Support", "Hacknet", "Libs", then "Injected"You should see "VMBootloaderTrap.dll" in the folder. Delete it File Location Windows: C:/Users/[YourUserAccountHere]/Documents/"My Games"/Hacknet/Libs/Injected Mac: [YourUserFolder]/Application Support/Hacknet/Libs/Injected This can also be done using your File Explorer/Finder. You just have to navigate to the same folder and delete the file. You might have to change your settings to view hidden files to do this, however. NOTE: This can happen more than once. My first playthrough, I had to go through the cmd prompt and I had no other issues. My second playthrough, I was able to use a trap to stop the first one, but the trap didn't work for the second try. The process for fixing it is the same, though. It Follows Connect to the given IP and hack in But there's nothing there! Not quite, my friend. Use MemDumpGenerator Use MemForensics on the generated mem file. To do this, go to your PC. All generated mem files are stored under /home/MemDumps Process recent commands run Go to the mail server and log in. Username: cornch1p Password: SaltyChippies22 Poke around the emails and look for new IP addresses Connect and hack into TortillaVPS Destroy all files in /home Cleanup Connect and log in to the IP using the informatio D3f4ult gives you. You can hack in, too, if you feel like it We're looking for unreleased music. There are two mp3 files here; both are in the /home folder. Find them and upload to the drop server Move back into the /home folder. See all those files that start with "d3f"? Those are D3f4ult's. Delete them Clear the logs Neopals Connect to given IP and hack in Scan for connections Connect to the Version Control server and hack in Browse the records. You'll notice that the ones with a * next to them have new IP addresses Hack in to Thomas Office. He has a txt file where he complains about Tiff storing her login information on her phone Hack in to Tiff Doehan's Personal Powerbook Use eosDeviceScan and log in to Tiff's ePhone 7 Get information from /eos/notes/work_logins.txt. You'll get the login for the Authentication server. Username: admin Password: mlk3fsdie321 Log in to the Authentication server. You'll see a text file telling Alex to stop writing admin passwords down there and that the offending file was deleted. Use MemDumpGenerator Process Files in Memory Username: admin Password: n8u5v432kj Log in to the Mainframe Go to /Database/Minx_x1.rec Replace the number of NeoPoints with a large enough number Bean Stalk Connect to the given IP and hack in Get Asdis Dagrunsdottir's IP address from /home/connections.txt There's a file in /home saying that all legal documents are kept on a cloud. You gotta look somewhere else. Use MemDumpGenerator Look at the mem file you get. Process recent files. You'll get a new IP address for someone named Manananggal Connect to their IP and hack in There's a file in /home/dagrunsdottir_leak. Grab it and upload it to the drop server Expo Grave Get all IPs from the mission description Go to the upload server and get the two files you'll need Hack in to Howard Grave's PC He has a copy under /home. Remove and use "upload" to replace with the matching file from the upload server In /home/phone_reminder.txt he mentions he changed his phone's login details. Username: admin Password: fma93dK Use eosDeviceScan and the new information to log in to his phone He has another copy of it in /eos/STORAGE. Remove and replace Connect and hack in to the Expo's server They have a copy under /home/talks/files. Remove and replace The Keyboard Life Connect and hack in to the given IP Open up /home/records/purchase_blacklist.txt Remove ChucklingKumquat from the list Take Flight Get both IPs from the mission description You can't just hack in to the Bookings Mainframe, so connect and hack into LAX_Pacific_Server Scan the network Connect and hack into the Network Hub Scan the network. At this point your team will get to work on taking out the Whitelist server. Wait a little bit and it'll be taken down You can now easily hack in to the Whitelist Authenticator Scan the network to get access to lots of employee computers Hack into Faith Morello's laptop Get PacificPortcrusher.exe from /bin Check out /home/work/logindetails.txt for her login information to the security IRC. Username: faithless Password: catsarebestpet Hack in to Vito McMichael's Laptop Go to /home/irc_address.txt and get the IP for the Security IRC Log in using Faith Morello's login details Look at the IRC chat and you'll get Yasu Arai's old password. It's "1185JACK" Hack in to Kim Burnaby's Office Computer Her eosDevice is corrupted, so get her email login from the backup under /home/ePadBackup. Username: kburnaby Password: noneofyourbusiness Go to PacificAir_Mail and log in using her information She'll have an email from Yasu Arai where he's complaining about security. Use the information in it to figure out his new password. It's "1185JACK1" Use that to log in to Yasu Arai's eBook Touch Use eosDeviceScan. Connect and log in using default information Arai's email login info can be found under /eos/mail/YasuArai@pacificair.com.act. Username: YasuArai Password: 9NINETWO2 Go back to the Bookings mainframe and click "PacificAir Bookings Mainframe" to get to the regular admin login. There's an option to reset the admin password. Hit it The new password will be sent to the administrator's, Yasu Arai's, email Go back to PacificAir's Mail Server and log in as Yasu Arai. The top email will have the new password, which is randomly generated Go to your mission description, add the password as a detail, and complete Take_Flight Cont. Get all the IP addresses from the mission description Hop over to the upload server and pick up sysinfo.bat under /home Connect to Pacific_ATC_RoutingHub and hack in. WORK QUICKLY Scan for connections. You'll see a new authentication server: Pacific_ATC_WhitelistAuthenticator You can't hack into the WhitelistAuthenticator, but you can use MemDumpGenerator on the RoutingHub. Do so Use MemForensics on the file you get from that Process recent files. You'll find the active whitelist password. It's CKYX258 Pacific_ATC_WhitelistAuthenticator is the active whitelist. Use that password to log in as the admin You need the authenticator to stop blocking you. There are multiple ways to do this: Make it think that you're an okay IP address: (Thanks to El Barbas for letting me know about the append command)Go to /Whitelist/list.txt Replace the IP address there with your IP ("replace [file text] [your IP]") or add your IP into the file ("append [file name] [your IP]") Removing the IP address when you're done is optionalTake the authenticator offline: (Thanks to Chewy for telling me this:)Find the authenticator dll Rename it to something else Forkbomb the authenticatorYou can now connect to Skylink. Do so and hack in as you usually would. WORK QUICKLY Upload sysinfo.bat from your PC to Skylink's /sys folder NOTE ON AUTHENTICATORS: "Why do I have to add my IP to the whitelist this time when I didn't have to do it during Part 1?" Part 1's authenticator had a whitelist, but it was disabled by your team. This one is still running, which is why you have to find a way to work around it. The Plane You have a choice. SAVE THE PLANE: Hack in to _0018 Grab 747FlightOps.dll from /FlightSystems Connect and hack in to the other plane (_0022) Upload 747FlightOps.dll to that plane's /FlightSystems folder Move to the plane's main page and hit "Reload Firmware". Hopefully you were quick enoughCoel will then ask you to go after Kaguya: Connect to the given IP and hack in Destroy everything. Take a look around if you wantWhen you've done that, Coel will give you something to turn everything back to normal. The Kaguya Trials are over. STOP THE PLANE: Don't do anything for _0022, or take too long to save it You can crash _0018 or not. It's up to youKaguya will then post an address to Kaguya_Projects. Hit the button, and everything will go back to normal. The Kaguya Trials are over.
尽管已经有许多关于《黑客网络》全成就获取方法的指南,我还是决定制作一份自己的。 这是一份逐步指南,旨在帮助你获取《黑客网络》中的全部11个成就。 介绍 大家好。 …… 欢迎阅读我的《黑客网络》全成就获取指南! 我将成就按完成度从高到低进行了有序排列,你可以直接跳转到你想了解的成就部分。 【Entropy】 获得Entropy账户 --- 1. 入侵Entropy测试服务器 2. 执行scp Entropy_Induction_Test命令 3. 入侵Slash-Bot新闻网络 现在你有一个选择。 4. 执行rm config.sys命令 或者 4. 执行mv config.sys "任意名称"命令 无论选择哪种方式,你只需对MsgBoard文件夹中的"config.sys"文件进行操作即可。回复邮件“Confirmation Mission”,你应该就能获得该成就。如果没有获得,继续推进剧情即可。就是这样。 CSEC 在CSEC内获得一个账户 无论你是通过Entropy还是/el/,这都无关紧要。 1. 入侵www.cfc.com 2. 那里什么都没有!进行扫描。 3. 入侵CFC公司主机 4. 没有任何关于11种秘密香草和香料的内容!进行扫描。 5. 入侵CFC记录库 6. 复制Seasoning_Order_Placement_Template_Pt1.docx和Seasoning_Order_Placement_Template_Pt2.docx 7. 将这两个文件上传到CSEC投递服务器 之后你应该就能获得该成就。如果没有,继续推进剧情,你会获得的。 Makeover! 运行ThemeSwitcher。加入CSEC后,你会收到一封邮件,邮件中说明资产服务器上现在有一个名为【ThemeSwitcher.exe】的程序 1. 连接到CSEC资产服务器 2. 传输【ThemeSwitcher.exe】 3. 使用命令【ThemeSwitcher】运行主题切换器 :P To the Wire 在还剩不到半秒时断开被追踪系统的连接 这个成就比看起来简单。 1. 连接到任何有追踪的系统。我最喜欢的是CCC Hacksquad Filedump 2. 探测并开始入侵 3. 现在,等待。 4. ... 5. 当计时器开始频繁发出提示音时,你可能需要输入命令【dc】 6. 快输入命令!!! PointClicker 购买PointClicker的最终升级 非常简单的成就。 你需要接受名为【PointClicker】的熵任务 1. 创建PointClicker账户 2. 入侵PointClicker 3.找到你的存档。它应该是[你的用户名].pcsav 4. 编辑你的点数。比如,给自己1000000000000000点。 5. 现在你应该可以购买PointClicker的最终升级了。在PointClicker的升级列表中向下滚动,因为升级项目很多。 黑客网络 完成Bit的最终请求 --- 基本上,就是通关游戏。 1. 连接到Porthack.Heart 2. Porthack Porthack? 3. 制作人员名单。你已通关游戏。 你最好不是靠点击获得这些点数的…… 拥有数量极其庞大的PointClicker点数 --- 与PointClicker成就类似。 你需要接受“PointClicker”熵任务 1. 创建PointClicker账户 2. 入侵PointClicker 3. 找到你的存档。它应该是[你的用户名].pcsav 4. 编辑你的点数。给自己设定999999999999999999999分。现在你应该获得了成就【Quickdraw】。 快速完成教程:比正常情况更早完成教程 好的,这个成就的获取方法可能有点难解释。 1. 创建一个新账户。 2. 开始教程,一直做到连接到与你相连的节点。 3. 现在输入命令“ps”。 4. 然后,输入命令“kill [教程进程编号]”。 你成功了!你“杀死”了一段代码!
/el/ Sec Champion Master of /el/'s friendly community --- This will go over EVERY STEP of /el/ 1. After you get hacked, connect to Naix Root Gateway. 2. Hack Naix Root Gateway PAYBACK! 3. rm x-server.sys 4. Hack Nortron Security Web Server 5. VANDALISM!!!!! replace "Nortron Security Services" ♥♥♥♥♥ 6. OOF! You're still not done! 7. Reconnect to Nortron Security Web Server 8. SCAN! SCAN! SCAN! 9. Hack Nortron Internal Services Server 10. Quickly scan, you're on a timer. 11. Hack Nortron Mainframe 12. You're in /el/. Now, you have 2 missions, and you have to complete both. I'll split the path now. Shrine of the Polar Snake Shrine of the Polar Snake? (Seriously?) 1. Hack Shrine of the Polar Star (IP is in the first thread, or here: 103.31.7.34 ) 2. Hmmm.... nothing here. Let's look in the source code. OOOH! 4 IPs! 3. Hack Trial of Patience (SOOOOOO SLOOOOOOW) 4. There's a number! Remember it. 5. Hack Trial of Haste (JESUS CHRIST THAT TRACE) 6. There's a number! Remember it. 7. Hack Trial of Diligence 8. Hmmm..... nothing. SCAN! 9. Hack Tail of Diligence 10. There's a number! Remember it. 11. Hack Trial of Focus (OMG THAT FIREWALL SOOOOO SLOW) 12. There's a number! Remember it. 13. Do you remember all your numbers? Or you can just look here: 103 33 8 162 14. 4 numbers.... Type in an IP, going in order from Patience, Haste, Diligence, Focus. AKA this IP: 103.33.8.162 15. Hack Head of the Polar Star 16. scp SQLBufferOverflow.exe Yay! That's one mission down. SecuLock Drive SecuLock Drive (AKA COME AT ME /EL's Secure SecuLock Drive) 1. Connect to COME AT ME /EL's Secure SecuLock Drive (IP is in the second thread, or here: 69.172.201.208 ) 2. 4 ports. If you did Polar Snake, hack in and rm DeleteMe.txt. If you haven't, keep following. 3. There's another computer IP in the thread. 199.89.130.68 4. Hack Stormrider 5. Nothing of use! (I guess WebServerWorm.exe is of use... though.) Wait. DriveSync.txt has something. Mica's ePhone 4S? 6. eosDeviceScan... 7. Get in Mica's ePhone 4S Username: admin Password: alpine 8. Let's check out notes. 9. Ooooh! Password! ithoughtyouweremakingtea 10. Connect to COME AT ME /EL's Secure SecuLock Drive 11. Login as admin - with password ithoughtyouweremakingtea 12. rm DeleteMe.txt TRUE ULTIMATE POWER Run Clock.exe --- OMG CLOCK.EXE IS A VIRUS - BUT CAN HACK INTO ALL COMPUTERS ES9EJG093T093HG09HWEG (Just kidding...) 1. Hack into Jmail. You heard me right, hack into Jmail. 2. The account dlocke has some interesting emails... YunaFan420?!?!?!!? WTF? 3. Hack Timekeeper's Vault No, the password is not yuna IP: 24.43.69.78 4. scp Clock.dec 5. Decypher Clock.dec with the password YunaFun420's favorite Final Fantasy character (and password to Clock.dec) is... Tidus! (Just kidding, it's Yuna - all lowercase) OR you could just DECHead Clock.dec 6. Move Clock.exe to the /bin/ folder - for some reason it goes to the /home/ folder. 7. Run Clock.exe Congrats! You are now connected to a botnet! That /el/ guy was right! Rude That's just impolite --- Uh oh, I'm going to get censored hard on this one. 1. After Naix hacked you, you reply to his email with ♥♥♥♥ you or anything with the word ♥♥♥♥ 2. Naix will reply back with: Yeah, ♥♥♥♥ you too, buddy. NOTE: YOU CANNOT GET TO /EL/ IF YOU WERE RUDE. Another note: Steam censors the certain word, so I'll tell you to reply with a 4 letter word that starts with f...
Full spread with pre-requirements for completing successfully the bit missions and finnishing the game. Prequisites For successfully completing the mission you will need the following programs on your local bin folder: SSHcrack.exe (first program achieved on bit's requests at the start of the game) FTPBounce.exe (second program achieved after completing the "Entropy registration" contract) eosDeviceScan.exe (third program achieved after recieving the "eOS device scanning" contract) SMTPoverflow.exe (fourth program achieved after you recieve the contract of "Agression must be punished") WebServerWorm.exe (fifth program achieved after you have naix's secondary relay server [from where he attacks you]) Sequencer.exe (sixth program achieved after you get accepted in CSEC) SQL_MemCorrupt.exe (seventh program achieved after you get accepted in CSEC) Decypher.exe (eigth program achieved in the "Ghosting the vault" contract) DECHead.exe (ninth program achieved in the "Through the Spyglass" contract) KBT_PortTest.exe (tenth program achieved in the "Project Junebug" contract) TraceKill.exe (eleventh program achieved in the start of bit's missions sent by "V") Another way to get the KBT_PortTest.exe after you have started bit's mission.Hack into the Universal Medical Server, search for a patient with "Whit Elliot", and then in the record find the "documentation and notes" IP. Here is the ip if you can't find it: 66.96.147.84. When you enter that server, click exit and hack the system. Firewall Solution For the server at 66.96.147.84 and it's adjecent one: BIOGEL. Once you are through, type scan and you will get another server (dont forget to delete your logs). Connect to that other server and hack it also, after you are through use "cd home/Production/Output" and copy the exe to your computer, then disconnect (dont forget to delete your logs here either). Now you have the tenth program ready. V - Bit -- Foundation This is the start of the missions, and it is simple, you download the TraceKill.exe after decompressing it with the given password dx122DX. once you have downloaded it, you just reply to the mail to continue with the missions. V - Bit -- Substantiation In here you have to connect to Bit's repo base (NOTE: TraceKill uses 600MB of ram, so if you want to stop the tracing you will have to get the ram free'd up and then run it [if you are running out of time after you have found the password {due to its long time to shutdown} simply shut it down manually with [b]"ps"[/b] and then "kill [PID]".]) Step 1: Hacking the systemStart by probing and getting the ports available for hack. You will have to hack/disable the following: (NOTE: You only need to open 4 ports to run porthack here) Proxy (overloading it with shelled computers) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) SQL Server (SQL_MemCorrupt in console, default port 1433) SMTP MailServer (SMTPoverflow in console, default port 25) FTP Server (FTPBounce in console, default port 21)If you do it fast, you should have some 30-40 trace time left, so run TraceKill as fast as possible for an extra time while you are in the server. In the server, you need to go to the directory ("cd home/work") home and then go in the work folder and copy the file in there. Disconnect and close tracekill and go to your pc, then analyze the .DEC file you just downloaded with DECHead. You will get an ip, put it in your notes or memoryze it, then reply to V with the IP adress. V - Bit -- Investigation You will recieve a mail from bit with another server, connect to that server, it's the main website of "EnTech". Start by probing and getting the ports available for hack. You will have to hack the following: (NOTE: You only need to open 4 ports to run porthack here) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) SQL Server (SQL_MemCorrupt in console, default port 1433) SMTP MailServer (SMTPoverflow in console, default port 25) FTP Server (FTPBounce in console, default port 21)After you are through (and porthack has shut down) run tracekill to get again some extra time. Start by scanning for linked computers, you will get 3 computers ("ZEUS", "WORKSTATION_CORE", "MAIL"), delete the logs (or have some fun around editing the website page cause you can) and disconnect from it (also shutdown tracekill after you disconnect). ZEUS and the MAIL servers are INVIOABLE so you can't hack them, you can only log in if you have the password, however you can hack the WORKSTATION_CORE. Probe the WORKSTATION_CORE. You will have to hack the following: (NOTE: Tracing here is very fast, so after you get the password manually kill porthack process and run tracekill as fast as you can) SQL Server (SQL_MemCorrupt in console, default port 1433)After you get the password and get tracekill active, scan the network for linked computers and delete your logs, then disconnect and shutdown tracekill. On the scan you will get 5 servers listed, 4 of them have the INVIOABILITY detection warning, but one of them doesn't. Connect to that sysem and probe it. You will need to hack the following: Proxy (Overloading with shelled computers) Firewall (Solution: BEKX4S [EDIT: According to a comment this now changes. You will have to figure this one out on your own if so.]) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) Medical Services (KBT_PortTest in console, default port 104)Once you have hacked through and activated tracekill, navigate to workstation > store ("cd workstation/store") and read "StoreServIPs.txt" to get the ips of the PROMETHEUS and ROMULUS servers. write both of them down in your notes, then read the file "Prometheus.txt" for the password to access the PROMETHEUS server. Once you have done this, disconnect (because there are no more linked computers to that last server) and reply to V's mail. (NOTE: if you can't reply to V's mail because it says mssion incomplete after following this whole secton from top to bottom, then check that the last mail that you recieved is V's mail about investigating bit's case, however, if it still doesn't let you reply, connect to the PROMETHEUS server and log in, at that point V should send you a mail back automatically.) V - Bit -- Propagation You will recieve another e-mail with a link back to the first found INVIOABLE system. Ignore it for now, you have to do something else first. Connect to the Prometheus server that you remembered/placed on your notes, log in with username: admin and the password that you also remembered/placed on your notes. Once you are in, delete the logs and run eosDeviceScan, you will find 2 linked phones. Connect to the first phone, and log in with the username: admin and password: alpine and go into the mail folder under /eos and write down in the notes the account username (what goes before the @) and also the password for the account. Disconnect from the phone and connect to the MAIL server of EnTech, log in with the username that you wrote down and the password for it. Once you are in the e-mail, read the mail that says "Re: Romulus passwd", copy down on your notes the password and disconnect from the mail server. Now that you have the ROMULUS password, connect to the romulus server and log in to it with the username: admin and the password that you placed on your notes. Go into the file system data and find a file under STORE/contractors named Contractor_Server.doc, read it and there should be a password again, write it down in your notes and disconnect from there. From here you can choose to go into the relay server (that V linked you and that is linked in the doc file) or reply to him with the password, you choose. V - Bit -- Vindication This part is simple, you get a mail from V telling you the password of a .DEC encrypted file in the EnTech Relay server. Decrypt the file if you want and then reply to V. V - Bit -- Termination This one will be a complicated and fast paced one, better read the guide first unless you know how to do it. PrequisitesGet some shelled computers ready (I normally use 6 for a fast proxy disabling). Step 1(NOTE: if you do not have Sequencer.exe downloaded, go grab it from the asset server.) Activate Sequencer.exe and click activate. Step 2You will be automatically connected to the offline server and you will be moved into the probe page automatically. You will need to hack the following: (NOTE: You need to hack it ALL to run porthack) Proxy (Overloading it) Firewall (Solution: [EMMETPLACE]) HTTP WebServer (WebServerWorm in console, default port 80) SSH (SSHcrack in console, default port 22) SQL Server (SQL_MemCorrupt in console, default port 1433) SMTP MailServer (SMTPoverflow in console, default port 25) FTP Server (FTPBounce in console, default port 21) Medical Services (KBT_PortTest in console, default port 104) Step 3Once you are in, you will have to navigate in the server ARCHIVE -> Hacknet and enter folder by folder and delete all the files in each with "rm *" Once you are done deleting that, delete your logs and ready up ForkBomb to launch it once log deletion is complete. You should be done with this and Sequencer should automatically close. Video Version:
步骤4:回复V的邮件,你会收到一封任务完成邮件。 比特-终端 这是“完成”游戏前的最后一个任务。